Another study found that international collaboration was positively correlated with the number of citations received by a research paper 54. Bibliometric analysis serves as a method to discern patterns, themes, and shifts within a particular realm of research. It also facilitates the identification of the most prolific institutions, authors, and countries engaged in that research domain. Researchers employ bibliometric analysis to examine subjects and nations in their studies 30, 31, 32,33. One of its notable advantages is its transparency, reliability, and ease of replication. In this process, it is also useful to carry out map visualization to analyze the structures of knowledge networks 34,35.
Complementary Tools

Despite being under legal scrutiny, Cracked.io remains one of the key hubs for those involved in cybercrime activities. On January 29, 2025, it was a primary target of Operation Talent, a law enforcement initiative coordinated by the FBI in conjunction with international agencies. That same operation also took down Nulled.to, another well-known forum, and both of their domains were seized by authorities. Founded back in 2008, Altenen suffered a major blow in 2018 when its creator was arrested and the original forum was shut down. RAMP enforces extremely strict access policies, with one key requirement being a solid reputation on other well-known forums like XSS or Exploit.in.
Best Onion Sites By Category
However, infiltrating criminal networks on the dark web requires meticulous planning and operational security to avoid compromising the investigation. On the dark web, insider trading networks operate covertly to evade detection by law enforcement and regulatory organizations. These networks might be quite sophisticated, with carefully planned and synchronized operations. Insider traders, hackers, and data brokers collaborate to share information, create trading strategies, and execute transactions. On the dark web, insider trading is significantly facilitated by hackers.
Real-World Applications Of The Tor Network
- Its primary focus is credit card fraud, although it also covers topics like cracking, hacking, and various aspects of IT and cyber scams.
- Pairs of users in stable pairs meeting inside a DWM traded for a total of $145 million in 2020, which corresponds to 252% of the 2019 level, and to 593% of the 2018 level, see Fig.
- You can access deep and dark web data through our dark web API and perform detailed data analysis with Lunar.
- As a result, it not only focuses on the UK but also provides worldwide news.
- You will find all the necessary .onion links to access any content or service on the dark web.
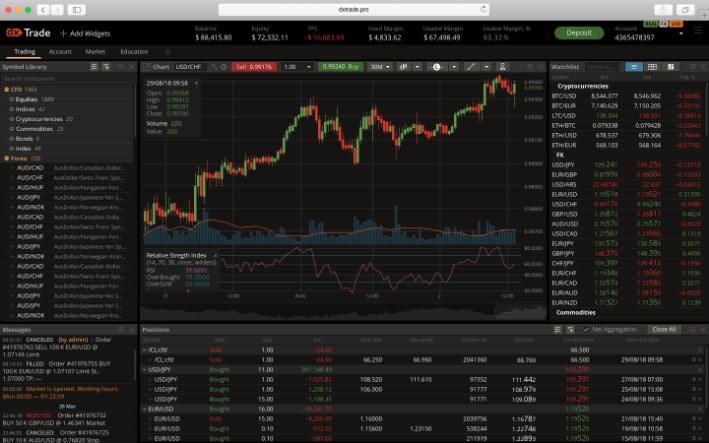
Fraud, manipulation, legal risks, and cybersecurity threats make participation in this domain perilous. Forex trading is generally conducted through broker platforms, financial institutions, and electronic trading networks. Its accessibility, leverage options, and 24-hour operation period make it attractive to both retail traders and institutional investors.
Author & Researcher Services
As such, they are normally under intense scrutiny from law enforcement and security professionals alike. Cybercriminals frequently exploit the dark web’s anonymity to launch scams, distribute malware, or conduct identity theft. In some instances, however, law enforcement agencies have been able to uncover the identity of those responsible for Dark Web insider trading. By taking advantage of advanced analytics, sophisticated digital forensic techniques, and other investigative tools, investigators can often trace back these trades to their origin and uncover who is behind them. Additionally, confidential informants and witnesses are invaluable resources in helping to determine the parties responsible for these securities violations.
Dark Web Links: The Best onion And Tor Sites In 2025
Due to their promise to allow for anonymous transactions, cryptocurrencies initially garnered appeal on the dark web. Since then, several criminal enterprises have begun to make greater use of cryptocurrency, including insider trading, ransomware attacks, and the distribution of illicit substances. Insiders who are eager to divulge confidential information may be persuaded by promises of financial gain or extortion threats. Dark web criminals regularly look for those with inside information to use their positions for nefarious financial advantage.

Ask Your Trading Data
Through statistical analysis, the article presents data on Silk Road transactions, shedding light on its user demographics and the reasons behind its popularity. Additionally, it discusses the legal implications surrounding the Silk Road’s operations, emphasizing the challenges law enforcement faced. Finally, the post reflects on key lessons learned from the Silk Road that could inform the development of future online marketplaces, highlighting the balance between innovation and regulation.
Early Warning Signals For Predicting Cryptomarket Vendor Success Using Dark Net Forum Networks
Addressing this issue, researchers 7 have successfully demonstrated the use of LDA (Latent Dirichlet Allocation) and a non-parametric HMM (Hidden Markov Model) to spot anomalous behaviors. Their techniques identified popular discussion topics in the Darkweb and diagnosed a state transition or change in topics bound to happen around any unique event. Going beyond the topics of interest, the need to identify perpetrators directly benefits law enforcement. While authorship identification using Artificial intelligence techniques has been explored in the literature, this has yet to be attempted for Darkweb. These objectives have been addressed by building authorship verification and identification datasets and exposing the challenges of using NLP techniques 8.
Economic Flows And Money Laundering
For example, an insider or factory employee might quietly slip away with an unmarked gun and sell it online. Once it lands on a darknet marketplace, it becomes part of the illegal weapons trade. It has a search option to let you find local and international products and services on the dark web. A lot of vendors from all over the world are registered here, offering an extensive range of products, including digital services, security tools, and other equipment. For those who are looking for a reliable Alphabay Market alternative, Awazon Market aspires to become the solution. Now, that is not to say illegal behavior is completely beyond detection.
Often portrayed as the internet’s shadowy underbelly, the Dark Web hosts marketplaces offering everything from privacy tools and digital currencies to more questionable, or outright illegal, products and services. Previous analyses of U2U trading relationships around DWMs include only two studies21,22 based on unstructured21 or semi-structured22 interviews of 17 users of Silk Road and 13 sellers on various DWMs, respectively. Here, we dramatically extend previous work by exploring the collective emergence and structure of U2U pairs.
Money Laundering
This extra privacy makes it much harder for authorities to track down who runs these markets and where they are located. For these reasons, most of these stores naturally like the dark web due to its protection. Purchases through links on our pages may yield affiliate revenue for us. We review and list tools and products without bias, regardless of potential commissions.
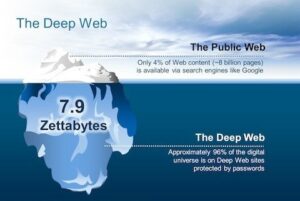
This hides the user’s original IP address and makes it extremely difficult to trace activity back to its source. Marketplaces specializing in the sale of stolen credit card information, login credentials, and compromised personal data. Prices vary depending on the type of data, its freshness, and the available credit limit. Commerce on the deep web has evolved from its rudimentary beginnings to become a parallel economic system with its own rules, trust mechanisms, and market specializations. A VPN protects your connection against everyone, not just your ISP and the authorities.