The best way to find out is to check the “Have I Been Pwned” (HIBP) website. This...
Plus, controlling access to the dark web would be a massive undertaking. For its part, Mullvad says...
This guide offers a comprehensive overview of the steps involved and the tools required. The darknet is...
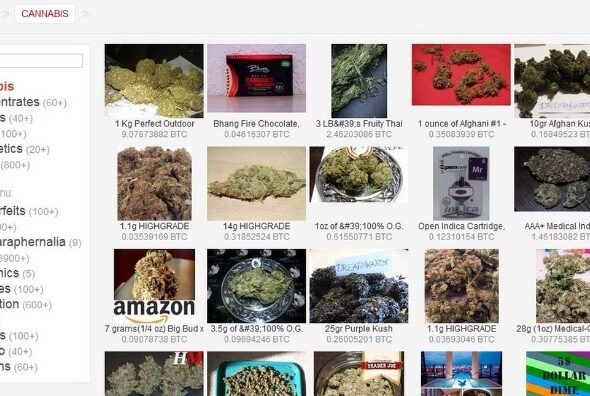
Darknet markets operate within this hidden space, often hosting illegal activity, while the deep web primarily consists...
ExpressVPN is consistently regarded as a top VPN service by multiple reviewers, such as CNET, The Verge,...
However, it is often prohibited for ISPs to sell your data to third parties. Many turn to...
And if you liked this article, follow us on LinkedIn, Twitter, Facebook, and YouTube for more cybersecurity news and topics. Great life...
The website is available on the surface web and has a .onion site. This means you can...
Right-click on the downloaded file and select “Extract Here.” Once the Tor Browser setup files have been...
On Android, you need the Tor Browser, and on iPhone, you need the Onion Browser. It also...