If you are an OSINT or information professional, having all these tools in your shortcuts will pay...
engines
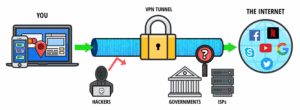
ActiveX and Java frameworks are susceptible to being exploited by hackers. Since you are navigating in uncharted...
Accidental leaks at the Tor entry nodes can potentially expose your IP address. A reliable, fast, and...
This allows whistleblowers to pass their information directly to those important news outlets. The great thing about...
The deep web is made up of email platforms, workplace portals, subscription services, and banking websites —...
This strategy has elevated Kilos to the status of a leading black market search engine. However, it...
LibreY stands out by supporting dark web image search, text results, and torrent links, making it user-friendly...