Search the web for lists of .onion sites and you’ll find some places to start. Many of the directories of .onion sites are themselves stored on .onion sites, though, which you can only access through Tor. For example, Facebook maintains an official Tor hidden services address at “facebookwkhpilnemxj7asaniu7vnjjbiltxjqhye3mhbshg7kx5tfyd.onion”. This allows you to access Facebook through Tor, and your connection doesn’t ever leave Tor where it can be snooped on. This may be useful in countries that block Facebook, for example.
Tips For Verifying Links On The Hidden Wiki
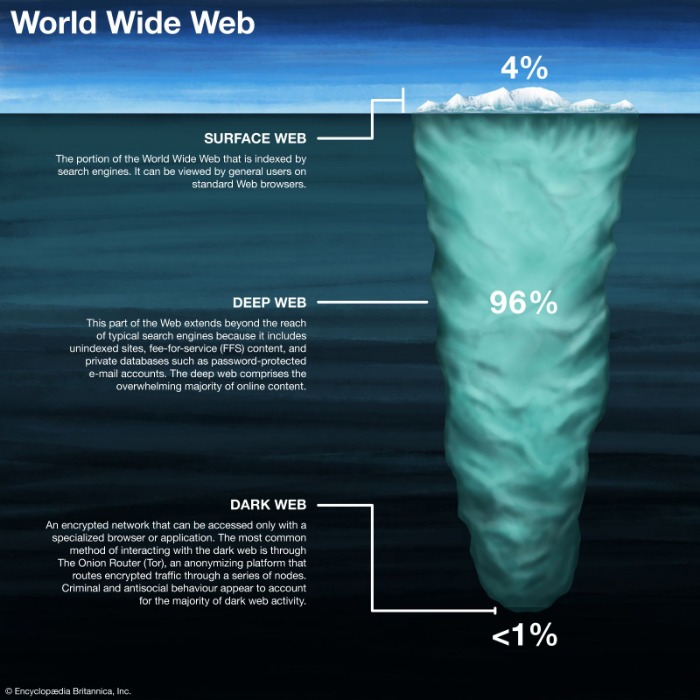
The Dark Web itself can be accessed through a special browser (TOR-The Onion Router) which bounces around IP addresses, constantly changing between layers, to protect anonymity. Your privacy, security, and legal compliance are solely your responsibility. We strongly advise robust security practices and strict adherence to all applicable laws. This site is for informational purposes only, offering no warranties or guarantees about the safety or legitimacy of any linked content.
ProPublica — Investigative Journalism News Site

The tale of Dark Web hitmen is more fantasy than fact — a chilling blend of fear, fiction, and fragmented truth. While the Dark Web does host illicit activity, the hitman-for-hire market is almost entirely composed of scams and law enforcement traps. Dark web researchers have long called the site a fraud, alleging that it is purely a vehicle to pilfer crypto from dumb but murderous Tor users. There are lots of marketplaces on the dark web, some of them specialized on drugs, others on murder for hire services, and others more general. The problem is you won’t really be able to search for them, so you’ll need to search yourself.
Biggest Google Breach Leaves 2,500,000,000 Gmail Users At Risk – Here’s How To Protect You

So, do yourself a favor and rescale that Tor window as much as you can before proceeding. Well, now it’s time to fire up Tails and do a little bit of tinkering. Chill, because nobody will ever find a record of you ever fiddling around the darknet. Note that Tails’ installation package is the .img format, which means that you’ll need software capable of burning images on your thumb drive. All you’ll need is an 8GB thumb drive, an installation package, and a couple of minutes to get things up and running. I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows.
Kingdom Market
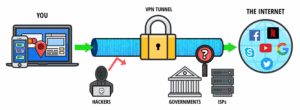
The stolen data included names, contact information, and order histories. Dark web listings surfaced almost immediately after the breach, advertising this information for sale to cybercriminals. This internet space can be dangerous but you can safely get on it by using a VPN and then connecting to Tor.
Conclusion: Safeguard Your Brand Against Dark Web Threats
Chainalysis says that $790 million worth of cryptocurrencies were used to shop in darknet markets during 2019. While some studies have claimed that illegal Bitcoin activity is as high as 44%. Check around with other users and ask if they know anything about the new marketplace. Government cyber teams can take such websites down, arrest the owners and then use the website to track and follow users that show activity on the website. Unfortunately, it’s also a place where the bad guys can offer their services – for example, hackers or hitmen. As I mentioned previously, the dark web is quite popular with journalists, political bloggers and news publishers, and others who run the risk of imprisonment in countries like Iran and others.

Private Internet Access
The platform is also used by governmental cyber departments to identify and track potential criminals or offenders. You can never be sure who’s really behind the other end of the line. Opennet connections are easier to use, but darknet connections provide more security against attackers on the network.
By doing so, they make it extremely difficult for law enforcement agencies to trace their online activities back to their physical location. Hitmen-for-hire is one of the most notorious services found on the deep web. These individuals, often referred to as ‘assassins,’ offer their services to anyone willing to pay the price. They claim to have the skills and expertise to eliminate targets without leaving a trace. The deep web provides a platform for individuals seeking to carry out illegal activities without being caught.
📚 Contents
- In addition to these tools, you need to exercise extreme caution when browsing on the dark web because there are tons of phishing and malicious sites on there.
- With advanced dark web monitoring, threat intelligence, and brand protection services, we help you uncover hidden dangers, prevent data breaches, and safeguard your reputation.
- Lastly, the dark web is the portion of the deep web that is generally inaccessible and is much larger than the surface web.
- So, I put together a list of the best dark web sites in 2025 to help you get started.
Many users rely on the Hidden Wiki to find reliable dark web resources safely and efficiently. This includes password-protected sites, private databases, academic journals, and, notably, dark web services accessible only through networks like Tor or I2P. The Hidden Wiki is a gateway to these deep web resources, offering links to .onion sites that cannot be found via Google or other surface web search engines. Thus, users who want to explore hidden, uncensored, or private content often rely on tools like the Hidden Wiki because it provides structured access to resources beyond Google’s reach. The Hidden Wiki is accessible primarily through specialized anonymity networks like Tor and, to some extent, I2P (Invisible Internet Project).
Through the dark web, users in places of high censorship can also access information and news. The reality is that hiring a hitman on the deep web isn’t only shocking but also extremely dangerous. The risks involved are significant, as individuals seeking these services can become victims themselves. Scammers and law enforcement agencies often pose as hitmen, leading to arrests or fraudulent transactions. Additionally, hitmen may be double-crossed or betrayed by their clients, resulting in retaliatory actions.
Verified Social Channels And News Sites
The social media giant is also aware of the many attempts by repressive regimes to restrict its access. After all, it enables users to connect and communicate with each other from around the world. Awazon became the successor of the popular AlphaBay market, which the authorities shut down successfully in July 2023.

Adding to that, the “know what you’re doing” is different from a regular browser in that altering the Tor browser settings can expose your private browsing data to external sources. You don’t necessarily want to use Tor all the time, as it’s slower than just browsing normally. But it’s a useful tool for anonymizing your Internet activity and bypassing censorship. Download the Tor browser from “torproject.org/download” and install it. Click “Establish a Connection,” then enter the “.onion” address you want to visit into the address bar. These sites are locked down so tightly that you need a special browser to access them.
BRspd, the hacker who in 2016 twice broke into Besa Mafia’s website, told me over private chat that he had approached Yura about turning Besa Mafia into an actual honeypot for criminals. In March 2017, they arrested David Crichton, a British doctor who had ordered a hit on his former financial advisor. Crichton did not pay the website, though, and later said he had put in the order just out of frustration; Crichton was cleared of any wrongdoing in July 2018. The Crime Bay website was eventually shut down by the NCA and the Bulgarian police in May 2017 and Monteiro assumed that Yura had been found and jailed.
It’s a precaution to protect yourself before diving into the dark web. For recommendations on choosing a VPN, look for expert reviews and articles. However, just like The Hidden Wiki, consider the links hosted there suspicious. While everything looks above board, there is no knowing if you’re heading to a phishing site, ready to steal your credentials, crypto, or otherwise. With Tor Browser, you are free to access sites your home network may have blocked.