
However, Tor’s most common use is to take advantage of its features to achieve a certain degree of privacy in web browsing on the internet. It is a private search engine that lets you search the regular internet via Tor. This allows you not only to visit sites with the added privacy provided by the Tor network, but also search the web as privately as possible from inside the Tor browser.

Anyone unfamiliar with the Dark Web should be extra careful, as some of the links in Hidden Wiki may be leading to suspicious websites. If you are looking for software resources, entertainment, sports, and financial information, The Hidden Wiki is the best place to gather all the initial information. No, conventional search engines like Google cannot be used to access the dark web. The platform includes a broad mix of content, from forums and marketplaces to privacy-focused resources, though it doesn’t filter out illegal sites, so caution is necessary. As a result, Torch is often considered one of the leading dark web search engines. It’s also important to note that your activities on the dark web aren’t completely immune to web tracking, and the expectation of anonymity can create a false sense of security.
BBC News (and Other Leading News Sites)
This information is invaluable for developers, researchers, and users interested in the technical and sociological aspects of the Tor network. Sci-Hub, often referred to as a “pirate” academic database, is a groundbreaking online repository that provides free access to millions of research papers and academic articles. With all of that in mind, you need to tread carefully when browsing, in terms of the sites you visit and the other users you interact with. Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place.
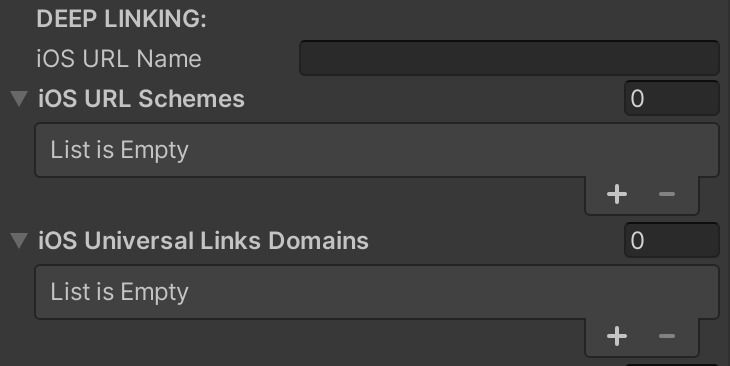
Boost Your Privacy When Browsing The Web With A VPN
In today’s digital era, where information is constantly on the move across all digital platforms, an… In addition, it has an automatic kill switch (Network Lock) that stops traffic if the VPN connection fails. Accidental leaks at the Tor entry nodes can potentially expose your IP address. You should never use your personal information on the dark web anywhere else in your life. Ensure you have used prepaid and unidentifiable credit cards when purchasing on the dark web.
Is The Deep Web Safe To Explore?
This makes it “invisible” to Google, but we can get this information from Deep Web search engines. Even if you try searching for .onion sites on Google, they won’t appear in the results because these sites are designed to remain hidden for privacy and anonymity. The problem is, the dark web isn’t indexed by regular search engines. KeyBase combines encrypted messaging with secure file sharing and identity verification.
Image Hosting — Upload & Share Images
Tor’s Hidden Answers is a raw, unfiltered, and anonymous platform reminiscent of Reddit. Unlike many other forums, it allows users to pose politically sensitive questions without fear of being banned. However, users should exercise caution, as discussions can quickly turn unsettling or disturbing due to the absence of community guidelines, oversight, or moderation.1. However, users should exercise caution, as discussions can quickly turn unsettling or disturbing due to the absence of community guidelines, oversight, or moderation. A censorship-free dark web platform where you can ask and answer questions anonymously.
Today, many organizations exist that are created only to handle these reports anonymously and effectively. They know how to process the information and get it to the correct law enforcement agencies internationally. If you are in a position to report the incident safely, you should report it to the authorities immediately.
Understanding Privacy Risks
- Always stay within legal boundaries and use the dark web responsibly.
- It’s the process of scanning dark web markets, forums, and .onion sites for specific identifiers, such as email addresses, passwords, or company data.
- LibreY is particularly useful for research purposes, as it provides access to resources often overlooked by other deep search engines.
- These onion domains are not indexed by search engines, so users can only access and explore the deep web through special software called “The Onion Browser” as TOR.
Its commitment to privacy and efficiency makes it a reliable tool for navigating the invisible web. To use NotEvil effectively, start by accessing it through the Tor browser for maximum anonymity. Use specific keywords to refine your search results and avoid generic terms that may lead to irrelevant pages.
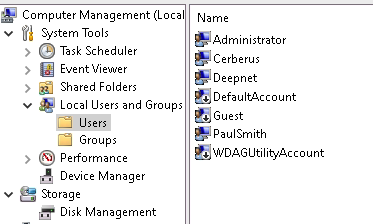
Can I Access The Hidden Wiki Without Tor?
Activists and government critics prefer to remain anonymous, fearing repercussions if their identities are revealed. Besides, victims of crime may want to hide their identities from their perpetrators. Nonetheless, if whatever you do is deemed illegal in your country, you can get into trouble. Therefore, the legality of the dark web will mainly depend on how you use it. You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom.

Dark web websites are hidden under layers of encryption that cloak user activity, which can be a boon to whistleblowers, activists, and others who don’t want anyone tracking their activity. There are many tor link lists, wikis and catalogues where you can find addresses to .onion sites. There are also many link lists in clearnet but majority of them is not updated and most links do not work. It’s standard that hidden services work for small amount of time and dissappear forever. Apart from the best onion sites listed here, you must be careful with the Tor pages you visit. Search engines and corporate websites might be OK, but even a popular Tor website like Hidden Wiki can show illegal deep web links that jeopardize your online safety.
Riseup is a volunteer-run collective dedicated to providing secure communication tools for activists and communities engaged in the fight for social change. Once you’ve got these two programs up and running, you can start browsing the dark web via the dark web urls we’ve shared. Some of the most common search engines and portals you can use to access the dark web are also listed at the dark web link collection above. It’s important you have one that you’ll use just for accessing the dark web links on this page. Once you’re there, you don’t know what kind of malware you can pick up, so it’s safer to use a new flash drive.
Since malware lingers across the dark web, your device can easily become infected, even if you are an unsuspecting user. In some countries, evading government restrictions to seek new political ideologies is punishable. For example, China uses the Great Firewall to block access to Western sites. Accessing blocked content can result in being placed on a watch list or imprisonment. All in all, it is not illegal to access the dark web, but it can create issues for you.
Venturing into the dark web highlights the need for robust data protection, not just for online activity, but also for your portable data. Just as you explore hidden corners of the internet, you need to secure your data on the go. Easily initiate data encryption on your external drives and disks, ensuring compliance with your specific company policies. Encryption-2-Go offers controlled encryption, container-based or directory encryption, and even detects existing BitLocker To Go encrypted drives. With configurable user selection dialogs, it provides a user-friendly experience while maintaining strict security.
The deep web or dark web is full of hackers offering their services. Dark web working logic We need to perform special crawling operations to index and index sites with .onion extension. It scans for keywords and topics and uses algorithms to deliver relevant pages. Use the AI chat feature to refine and personalize your presentation. This tool provides suggestions and enhancements, allowing you to create a polished final product. Agentic empowers you to turn abstract ideas into visually compelling presentations.



