
The Dark Web refers to a specific section of the internet that exists on an encrypted network, intentionally hidden and accessible only through specialized software. It forms a small part of the Deep Web, a term that encompasses all parts of the internet that are not indexed by traditional search engines. To understand the Dark Web, it’s important to first grasp the broader concept of the Deep Web.
Encrypted Communication Tools
The VPN is a second layer of extra protection, on top of the protection that the Tor network already offers. The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor. You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web. So, sites that contain a domain extension like .com, .org, .net, .biz, .info, etc. can be found on the surface web. In addition, the content on the pages don’t need any special or custom configuration to access.
The Dark Web: Risks And The Role Of Standards
We take a deep dive into what the dark web is and the dangers it poses. DuckDuckGo is the best dark web search engine, as it offers an excellent user experience akin to surface web search engines. Its effectiveness in scouring the shadowy depths of the dark web can be likened to what Google does on the surface web. After all, some websites on the deep web are like those on the open internet, except that they are hidden behind a paywall or protected via passwords to limit access. The “onion routing” technology underpinning the dark web was developed by researchers at the U.S.
Law enforcement officials can also set up traps to capture criminals engaged in illegal transactions. Subscription-based applications can be accessed only once the user has paid for them. The paywall prevents search engine crawlers from accessing this content. Examples include software as a service (SaaS) solutions, paid news websites, and streaming services. While they make accessing Tor-hidden websites easier without the Tor browser, they can compromise your privacy and security by acting as intermediaries that might expose your data.
- SecureDrop stands out as the leading platform for secure document sharing used by major news organizations.
- This includes personal email accounts, online banking portals, cloud storage, subscription services, and medical records — essentially, any page behind a login, paywall, or restricted access.
- The ‘members only’ parts of public platforms are also a part of the deep web.
- This helps obscure the origin of the data (and makes it hard for anyone to find your IP address).
- The terms dark web and deep web are perceived to be linked with illegal and otherwise suspicious activity; however, a vast difference exists between the two.
Dark Web Vs Deep Web Vs Surface Web
The dark web is part of the hidden web, which comprises non-indexed websites that are mostly used for illegal and illicit activity. If you have heard your peers or colleagues throw this term around and are wondering, “What is the dark web? The dark web is a controversial part of the internet, famous for being a hotbed for illegal and criminal activity. Read our comprehensive “what is the dark web” guide to understand how it works and the risks and benefits.
Method II – VPN Over Tor
Regular search engines only provide results from the most recent version of a website that’s available. Radar Rundown Private search engines use the metasearch or proxy search model and the proprietary cr… Accessing tunnels is illegal and dangerous, which is why records of these “adventures” can only be found on the dark web. If you want to access this site, do it only for fair purposes and with proper security measures.
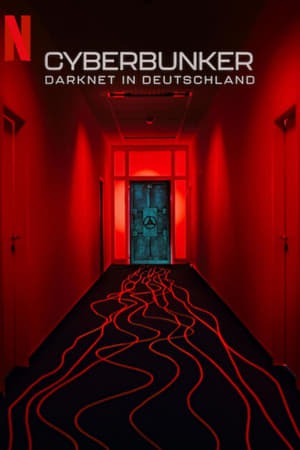
Since the site ran on Tor, which granted a high level of anonymity, users could trade weapons, hard drugs, and other illegal substances. Payments were primarily in bitcoins, further contributing to the site’s safety and security. You will find paywalled news articles, subscription sites, and private social media posts all live there. It’s not some shady underworld (that’s the dark web, which is a whole different thing). It’s just the part of the web that’s locked behind passwords, paywalls, or privacy settings. Indeed, Facebook, The New York Times and now even the CIA have sites on the dark web, hosting “onion” versions of their pages that can be accessed via the Tor browser.
Quick Links
When you search for something on Google or Bing, you’re using the clear web. That said, many of the actors on the dark web are highly skilled digital adversaries who can easily outmaneuver basic security measures. As a leading cybersecurity vendor, CrowdStrike cautions all organizations and individuals to refrain from using the dark web. The dark web continues to be a valuable tool and exchange network for many groups around the world. Some consider it an outright necessity, as it helps encourage free speech, maintain a free press, and support the work of law enforcement and government agencies. One we’ve encountered is a scammer pretending to be the admin of an exclusive forum we tried to sign up for.

Place a credit freeze or lock on your credit reports, monitor your credit reports and financial accounts closely for any unauthorized activity, and consider enrolling in a credit monitoring service. Additionally, contact the Social Security Administration to report the breach and discuss further protective measures. To help find functioning .onion URLs, look to dark web directories and forums — Reddit users recommend tor.taxi, tor.watch, daunt.link, or one of the Hidden Wikis. Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor….
Is The Dark Web Dangerous?
Since privacy and security are a concern while using the dark web, the websites you visit must have the encryption necessary (HTTPS, preferably) to protect you. The search engine has indexed over 400,000 pages, and you can ask it to match your exact search term. You can easily find what you are looking for, even links to hidden dark web rooms. With its nifty “conjoin” feature, users can combine different coins in one transaction, covering the user’s tracks and maintaining their anonymity. The wallet is user-friendly and provides robust security, making it one of the best crypto wallets on the dark web.
This connection methodology enables users to interact with the dark web with minimal risk of their activity being tracked or otherwise exposed. Interestingly, at the cusp of the new millennium by the US Naval Research Laboratory originally developed the Tor project. An early version of the Tor browser was created to combat the challenges presented by the lack of privacy during the initial days of the internet. Its main goal was to prevent spy communications from being discovered; however, the framework was eventually repurposed and made public.
What Is The Deep Web, And How Do You Access It?
- However, the main caveat is that the Tor network (an onion network that uses a series of nodes to provide you with access) is very slow.
- In the digital world, “Deep Web” and “Dark Web” often get mixed up, leading to misunderstandings.
- Finally, you need to enter website addresses to access content on the dark web since you can’t browse by entering a search query as you can on the clear web.
- For this guide, we’ll use the Tor Browser as an example, but any other web browser (like Brave) that supports the Tor protocol will work just as well.
Though the dark web offers anonymity for journalists and activists in oppressive regimes, it raises many ethical concerns. Knowing about various types of ransomware and common hacks can help you better prepare to spot cybersecurity threats on the dark web. This allows you to use the computer without the risk of corrupting your computer’s normal operating system with viruses or malware. Tails also protects you from possible malware, viruses, or keystroke loggers that may have already infected the computer, as it doesn’t run the operating system already installed on the device.
Cybersecurity Awareness: 10 Tips To Stay Safe Online
On Hidden Wiki, you can find working links to sites like ProPublica, Facebook, Deep Web Radio, and more. This requires your connection to go through multiple nodes and relays, which will slow down browsing on Tor. Copy your desired onion URL and paste it into the address bar at the top of the screen to begin searching on the dark web. Alternatively, if the website has turned the onion URL into a link, you can click on that in the Tor browser, and it will automatically open the dark website. As the digital world continues to evolve, the Dark Web will undoubtedly remain an important and often controversial part of the internet’s landscape.



