These forums can provide valuable insights into the workings of the dark web, as well as tips on navigating its complexities. Be wary of the content you interact with on the hidden wiki and other sites within the deep web. While many links can provide valuable information, some may lead to illegal activities or scams. Exercise discretion and always verify the trustworthiness of sources before engaging with them. However, you can trace its roots to the development of technologies like the Tor network or Freenet. In March 2000, an Irish grad student named Ian Clarke created the software application, Freenet.
The Hidden Wiki: A Comprehensive Guide To Dark Web Directories
- BlackCloud offers encrypted file storage specifically optimized for the Tor network.
- It scans darknet marketplaces and hacker forums to alert you instantly if anything shows up.
- Speaking of which, be very, very careful when slinging your digital dollars around.
- The New York Times can also be anonymously accessed via the dark web.
- It was created in 1999 as a secure communication platform for people and groups working on liberatory social change.
- Onion sites aren’t really dangerous, but they could be when accessed through unfamiliar or suspicious links.
|
- Its ongoing presence is also a testament to the resilience of the dark web community against censorship and takedown attempts.
- The anonymous group behind Tunnels alleged that the materials were produced while exploring the forbidden tunnels, built underneath some of the most prestigious American Universities.
- The rise of alternative discovery tools like darknet search engines or market review forums has supplemented but not replaced the Hidden Wiki’s role.
- Scammers and criminals are lurking everywhere to take advantage of the unwary.
|
- While popular email providers may be convenient, they often track user data, impose stringent monitoring, and may not be optimized for anonymous browsing.
- On the one hand, this is considered beneficial for people living under strict regimes where censorship is common.
- If you want to access this site, do it only for fair purposes and with proper security measures.
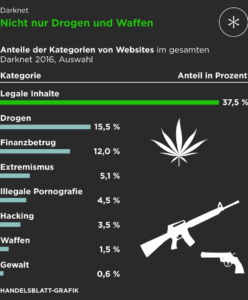
- The darknet and its marketplaces not only offer drugs, medicines, doping agents, online identities, credit card data, and false passports, but also weapons of all kinds.
- The Hidden Wiki doesn’t discriminate, so if you randomly start diving into the onion sites listed, you may come across objectionable or dangerous material.
- Onion websites use onion routing, a technique for encrypting and anonymizing data transmitted over the Tor network.
|
- There are also many tools that can be use to monitor the dark web and scan for personally identifiable information and even respond to attacks.
- Many of those sites are listed because their devs have submitted the site directly to the search engine for indexing.
- When you purchase through links in our articles, we may earn a small commission.
- Operating through Tor, DuckDuckGo provides a non-censored search engine experience without logging personal data.
}
This is because law enforcement often actively monitors these sites. Many dark net sites do not undertake the necessary measures to protect users like most websites on the surface web. As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing. Simply put, accessing and browsing the dark web is perfectly legal. For example, it maintains your privacy and enables you to access untraceable content and services.
Subscribe To The Blog Newsletter
Some may lead to malicious sites, downloading malware on your device. The dark web is not easily accessible, especially with browsers like Chrome or Safari, as it requires specialized protocols like Tor’s onion routing. As a result, the recommended browser for accessing the dark web is the Tor (The Onion Router) browser.
Best Dark Web Sites 2025 – Detailed List
Sellers migrate to invitation‑only channels or switch to encrypted messaging apps when a site goes dark; buyers follow reputation scores, not domain names. Law enforcement, meanwhile, leverages blockchain tracing, undercover buys and server misconfigurations to stage high‑impact busts that temporarily inflate prices and spur copycat platforms. Such spaces let researchers and activists trade defensive know‑how without exposing their real‑world identities. The project’s March 18, 2025 release (v2.12.0) added Ubuntu 24.04 support and a semiautomated upgrade path, underscoring its active maintenance and newsroom trust. Countries differ in how aggressively they monitor Dark Web activity. In some authoritarian states, accessing Tor nodes can flag you for surveillance.

News & Media
Onion sites are considered part of the deep web because search engines like Google and Bing can’t index them. Verify links using community forums or updated lists maintained by trusted darknet users. Be aware that many scam sites imitate legitimate ones, so use PGP signatures or other verification methods if possible.
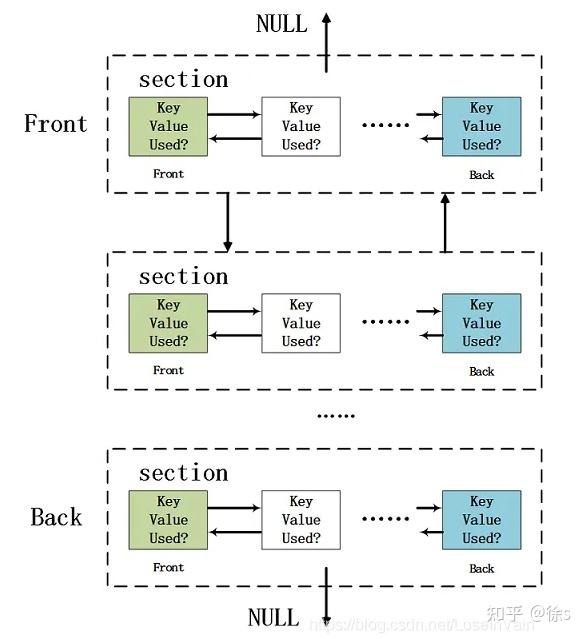
Quick Guide: These Are The Best Dark Web Links In 2025

Dark markets often employ end-to-end encryption for communication between buyers and sellers, enhancing security and privacy. This encryption ensures that messages cannot be intercepted and read by third parties, including law enforcement. The use of digital signatures can also help verify the authenticity of users and transactions. Dark markets, as well as various other services within darknets, are hosted as ‘hidden services’. This means that the servers providing these services are only accessible via Tor and do not have a public IP address or domain name. Hidden services can operate while keeping the physical location of the server hidden, which makes tracking and shutting them down considerably more challenging.
What Is The Hidden Wiki?
Venturing into the dark web highlights the need for robust data protection, not just for online activity, but also for your portable data. Just as you explore hidden corners of the internet, you need to secure your data on the go. Easily initiate data encryption on your external drives and disks, ensuring compliance with your specific company policies. Encryption-2-Go offers controlled encryption, container-based or directory encryption, and even detects existing BitLocker To Go encrypted drives.
Counterfeit Documents And Identity Kits
It adds an extra encryption layer and passes your traffic through a secondary server of your choice, preventing anyone from seeing that you are accessing the web via Tor. Immediately close your entire Tor Browser window (not just that active tab). Note that engaging with the content in any way is not only distressing but could also put you at legal risk.
In some countries, evading government restrictions to seek new political ideologies is punishable. For example, China uses the Great Firewall to block access to Western sites. Accessing blocked content can result in being placed on a watch list or imprisonment.
List Of Tor Onion Services
- One option is to try DuckDuckGo’s .onion version, which is great for privacy.
- In most cases, whistleblowers have sensitive information about the government or a company.
- It is known for strong encryption protocols and anti-DDoS protections, ensuring reliable access and user anonymity.
- With a readable site name like that, people will know what to expect when they click on the link.
His articles have appeared in many respected technology publications. Dark web forums are online platforms that can only be accessed using anonymous networks, mainly Tor…. This will help you to remain anonymous and secure at all Tor entry and exit nodes. It uses TrustedServer technology on the entire server network to wipe out your data after every session.

Stolen Data And Identity Theft

Using a VPN can help strengthen your privacy while visiting the dark web. While many dark web websites, like the former black market website Silk Road, are used to facilitate criminal activity, there are also plenty of legitimate dark web websites. Yes, you can access the dark web on a smartphone, but you’ll need an appropriate browser, like Tor browser for Android or Onion browser for iPhone. Remember that phones can get viruses just as easily as computers, and the chances of getting a virus likely increase when you’re browsing dark web mobile sites, no matter your platform.
The service emphasizes privacy with zero-knowledge encryption and no registration requirements. My tests showed reliable performance for smaller files, but larger transfers can be slow due to Tor’s limitations. Alt Address provides disposable email addresses specifically designed for dark web use. This service helps protect your primary email when signing up for .onion services. I found it especially useful for testing new services without risking my main email address, though messages expire after 24 hours. Whether you’re looking for personal advice while shopping on the dark web or you want to discuss a wide range of topics, Dread has you covered.