His idealistic vision of an open marketplace ran on libertarian philosophies and Bitcoin. To turn it on, just go to the “Settings” and then the “Tools” section of the NordVPN app and activate “Dark Web Monitoring.” In the end, it’s all about staying one step ahead. The more proactive you are, the better you can protect yourself against identity theft and other cyber threats. This explains how the market of the dark web marketplace is affected. As Telegram has end-to-end encryption and anonymous profiles, it makes it an ideal choice for threat actors and hackers to take advantage of. But these efforts of law enforcement don’t go in vain; hackers and criminals lose trust if a website or marketplace goes down.
How Do Scammers Get Digital Identity Information?
Ben Luthi has worked in financial planning, banking and auto finance, and writes about all aspects of money. His work has appeared in Time, Success, USA Today, Credit Karma, NerdWallet, Wirecutter and more. Not all personal information is valued the same on the dark web. Prices can vary based on demand, how complete the data is and how easily it can be monetized by criminals. First, in the USA, it is a federal offense to use the USPS for any of these transactions. If the buyer or seller gets caught, there are significant legal ramifications.
Fraudulent Markets
There’s also a supplier list categorized depending on their countries of operation. Topics cover everything from lab setup, production to encryption, marketing and legalities. It also covers the back-end aspects such as Pharmacology, health topics, minimizing self-harm etc. Registration isn’t required to browse the forum, most threads are open for all. Cash Cow sells PrePaid cards, PayPal transfers and Accounts, Bank Transfers, Western Union Transfers, MoneyGram Transfers, Real Money and Gift cards.
Identity Theft
You must register first if you’re a new user on this platform. At its launch, the platform accepted payments through Litecoin, but now it has incorporated support for other payment methods like Monero and Bitcoin. The platform also cares about its users and uses PGP encryption and two-factor authentication to secure their data and communication. Its intuitive interface and advanced search features make it easy to find local and global products. The marketplace extensively vets vendors listed within its deep web environment that offer a wide range of product portfolios, including security solutions, digital services, and specialized equipment.
Deep Money Transfers
Listing includes amount you will get, price and shipping time. Fast Money deals with prepaid cards, PayPal accounts, PayPal transfers, Western Union Transfers, MoneyGram Transfers, and CC Fullz. Each product has large amount which you can get by paying very low amount. All products are listed with the amount you will get and you need to pay.

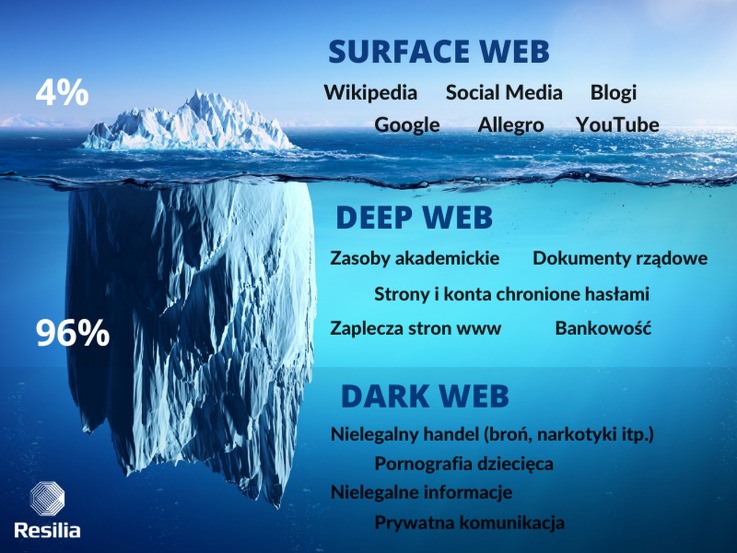
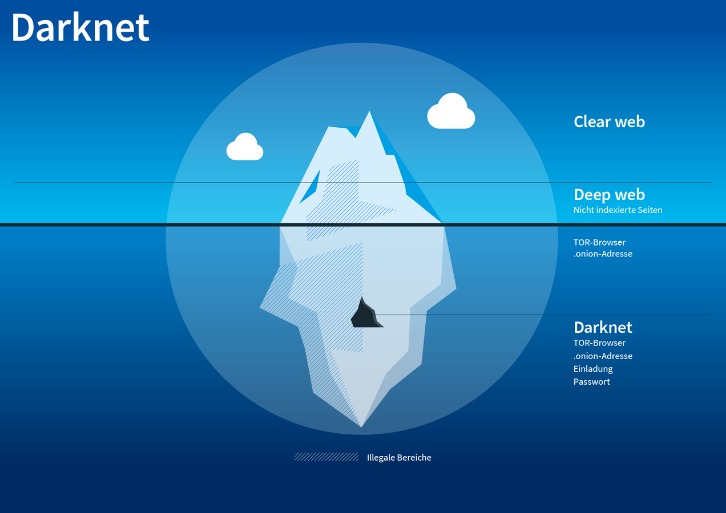
The same anonymity that publishers enjoy on the dark web can be utilized by users who want to read the available information. Again, people who live in countries where the freedom of the internet is limited, for example in China, can really benefit from using Tor. The deep web contains sites and pages that are often prevented from being indexed by search engines and contain unlinked content.
- Although channels are occasionally blocked, new groups are usually created within a few hours.
- First things first, always use strong and different passwords for each account you open.
- Flash BTC Software allows you to send BTC fakes on the blockchain network.
- It brings you prepaid EU debit cards and prepaid US debit cards.
- Buying illegal substances, stolen merchandise, and counterfeit currency or goods online poses significant risks for both the buyer and the seller.
- Data gleaned from ransomware and data breaches is available on the dark web.
Of course, not all activity on the dark web is criminal, but such marketplaces are where a lot of illegal trade and money laundering happens. By relying on encryption, pseudo-anonymous currencies, and network-level anonymity, they create a false sense of safety, drawing in both buyers and sellers. Our team searched the dark web and put together a list of the most active dark web marketplaces in order to assist you in monitoring illegal trade of products, cybercrime activity, and dark web trends in the dark web space. This marketplace specializes in a variety of illegal products, including drugs, counterfeit documents, and hacking tools. Some dark web marketplaces even host content that’s not just illegal but extremely harmful, so it’s really important to understand the risks before diving in. The first category includes classic marketplaces, which serve as one-stop shops for a wide range of illegal goods.
German onion Forum
Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts. Believe it or not, some dark web marketplaces have pretty advanced systems for building trust. Sellers often need to pay a deposit to prove they’re serious, and they build their reputation through positive reviews. The dark web marketplaces are mainly defined into two categories.
That’s why it has such a foreboding and even dangerous reputation. It is used by many for buying or selling items that are prohibited on the regular internet, like fake IDs, illegal drugs, and stolen data. Imagine an underground version of your favorite online marketplace, somewhere hidden, exclusive, and often operating outside legal boundaries.
Technical Risks And Identity Exposure
- As governments introduce new security measures, counterfeiters adapt quickly.
- We are an information site that readers like you support.
- Each country has different specific forms of identification, and all countries use a driver’s license as a general ID card — so both specific and general IDs are essential documents for new identity seekers.
- Future research could address these dynamics by employing several approaches.
- But again, your ISP won’t be able to see any of the content you’re reading or what you are sending and receiving through the Tor network.
In addition to the brief introduction of “fake” marketplaces on the dark web, dark web users visiting political sites on the Tor network should realize that government-funded cyber teams are on the lookout for such users. The invisible web is made up of data and information that is not indexed and cannot be searched for by using traditional search engines. Content includes non-indexed websites, apps, and resources, which can include protected information such as, online banking, specialized databases, non-linked and password-protected websites, and more. It includes media and archives which cannot be crawled and indexed with current search engine technology.

Ethical And Legal Boundaries In Monitoring Darknet Marketplaces
From drugs and fake IDs to hacking tools and weapons, these marketplaces promised decentralised freedom from the oversight of banks, governments, and corporate middlemen. Fake IDs and passports are predominantly sold through hidden online marketplaces accessible via the dark web. Individuals purchase fake IDs and other fraudulent documents for a variety of reasons.
Darknet markets operate within this hidden space, often hosting illegal activity, while the deep web primarily consists of everyday private or password-protected content. Even passive activity on these sites can contribute to criminal networks. For instance, buying fake documents may indirectly support larger operations involving trafficking, extortion, or organized crime. Dark web markets work much like regular e-commerce websites but with extra layers of anonymity and encryption. Buyers browse listings, place orders, and pay with cryptocurrency — typically Bitcoin or Monero — to obscure transaction trails.
Altcoin Boom 2025: Why Ethereum And Altcoins Are Surging Beyond Bitcoin
This really shows the vast impact nations and organizations are facing due to the identity and PII information being stolen, bought, and sold in the darknet markets. BidenCash became known for regularly leaking huge amounts of stolen credit card data and personal information — often for free. This strategy, along with a strict sign-up process, helped it grow fast. The goal is simple — make financial fraud easy and get as much attention as possible.
This could include their name, email, passwords, biometric details, or even device information. A woman in New Brunswick had her account hijacked; what started as a simple Facebook login ended with her friends being scammed out of thousands. The scammer used her digital identity by sending fake messages to her contacts, collecting payments fraudulently, and then disappearing without a trace. Law enforcement officers conducting routine traffic stops, public event checks, or investigations often detect counterfeit IDs through portable scanners and specialized software. Officers are trained to recognize physical inconsistencies like poor printing quality, incorrect fonts, mismatched data, or suspicious behavior. Additionally, verification against national databases can instantly identify fraudulent documents, resulting in immediate arrest or further investigation.



