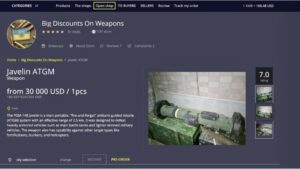
It contains a good selection of product listings that range over 35,000 items. It uses PGP encryption,...
darknet
Drainer developers are increasingly focused on serving their long-term clients, with most activity now conducted in invite-only...
When you try to connect to a .onion website, Tor will route your traffic through three or...
Hacked social media accounts are evidence that cybercriminals have a diverse appetite for Dark Web data products....
All of this underscores Riseup’s prioritization of users’ rights over business interests. ProPublica is independent, so you’ll...
This is an estimated reading time to let you know how long it will take you to...
Simple mistakes—such as inadequate operational security practices, sharing identifiable details, or using compromised devices—can quickly compromise anonymity...
Interestingly, new sites get more hype, and it even becomes difficult to shut them down, as they...
Don’t click on suspicious links, be skeptical of what you read, and avoid dark web marketplaces if...
For instance, in January this year, it was the target of Operation Talent, the law enforcement initiative...