If you want to buy something, deposit cryptocurrency in your wallet, and you will be charged directly....
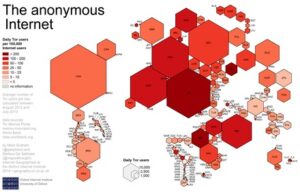
20 As noted in Figure B, there is a lag time between when the activity occurs and...
These can include the previously mentioned illegal offerings, but can also include ultra-private information designed to be...
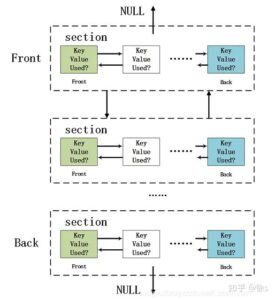
Some have implemented distributed hosting, robust compartmentalization, and enhanced privacy features to mitigate centralized points of failure....
We, therefore, use the following 4-step process to reduce the DWM dataset to a list of Bitcoin...
For instance, you can choose the preferred security levels for enhanced protection. The security level is set...
Any online activity can carry breadcrumbs to your identity if someone digs far enough. When viewed through...
Businesses may use these services to sabotage their competitors, while individuals may seek revenge or simply want...
In addition to tracking individual transactions, law enforcement agencies also focus on disrupting the infrastructure supporting illegal...
It is considered very secure thanks to strict user validations and transparent payment and vendor review procedures....