It’s an ever-evolving ecosystem—constantly shifting, reinventing itself, and adapting. Although some of these markets prohibit certain extreme content such as violence or exploitation, most operate with very few rules beyond ensuring the security and anonymity of their users. In mid-2024, Telegram confirmed cooperation with European authorities to remove clusters linked to ransomware extortion leaks. While takedowns rarely eliminate operations, they force constant churn and reduce the longevity of large-scale hubs. For defenders, monitoring communication platforms has become as important as tracking marketplaces themselves. DarkOde Reborn is a great darknet market where you can find anything you want.

How Dark-Web Marketplaces Operate In 2025
- Reflecting the versatile applications on Ethereum, the Lightning Network is now home to a spectrum of applications ranging from DeFi and NFTs to gaming.
- In a scenario where Bitcoin was mass adopted, this would mean that users and companies would potentially be able to see where and how users are spending their funds.
- Despite Telegram’s anonymity, the dark web is still a hot spot for illegal trading of malware, illicit goods, and stolen data (such as stolen credit card information).
- Saheed earned his degree in Technology and Ethics from the University of Lagos in Nigeria.
Buyers prioritize markets with real-time tracking and stealth packaging guarantees, which are now common features. The shift toward decentralized platforms has also reduced centralized server vulnerabilities, ensuring longer market lifespans. Reputation algorithms weigh recent transactions more heavily, preventing vendors from artificially inflating scores with old reviews. Markets optimize their escrow systems for Bitcoin, reducing disputes through automated smart contracts. Buyers benefit from lower fees during peak hours compared to Ethereum-based networks.
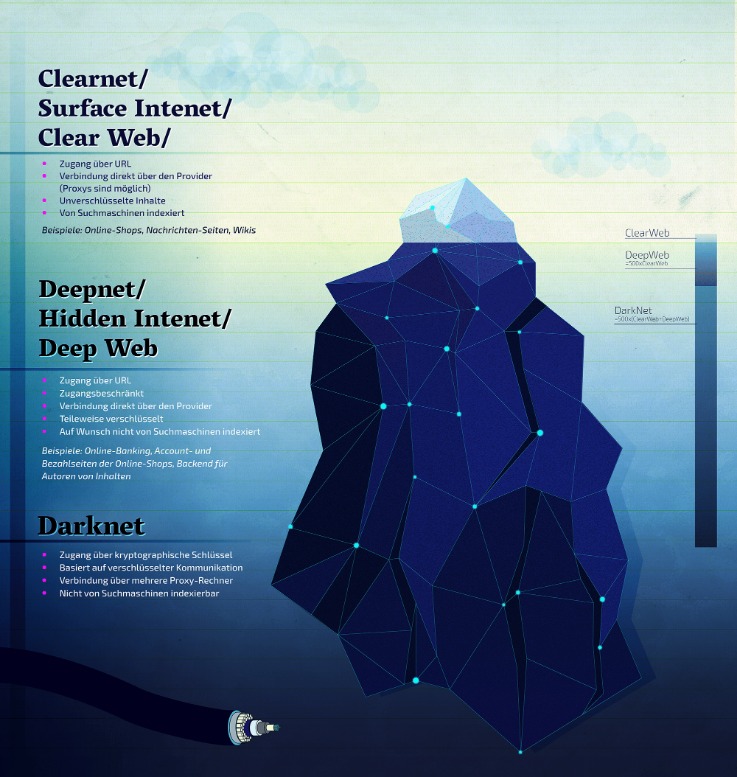
The Lightning Network is a peer-to-peer network made up of these nodes connecting to each other. Indeed, the more nodes open payment channels, the more total network liquidity increases which means that overall more users can send more money to more people. The darknet is a mysterious and often misunderstood part of the internet, attracting both intrigue and concern. Darknet markets, in particular, have gained attention for their role in facilitating the exchange of illicit goods and services. Despite their controversial nature, these marketplaces continue to evolve, offering a glimpse into the darker side of online commerce. As cyber threat intelligence professionals monitor these markets, they gain insights into emerging threats and malicious activities that can impact organizations and individuals.
Understand Crypto With Ease
The best way to understand how the Lightning Network works is to imagine you want to send Bitcoin to a friend. Instead of broadcasting the transaction to the entire Bitcoin network, you and your friend can open a payment channel on the Lightning Network. By creating a network of these two-party ledger entries, it is possible to find a path across the network similar to routing packets on the internet. The nodes along the path are not trusted, as the payment is enforced using a script which enforces the atomicity (either the entire payment succeeds or fails) via decrementing time-locks. Two participants create a ledger entry on the blockchain which requires both participants to sign off on any spending of funds. Both parties create transactions which refund the ledger entry to their individual allocation, but do not broadcast them to the blockchain.
Online Marketplaces And Platforms
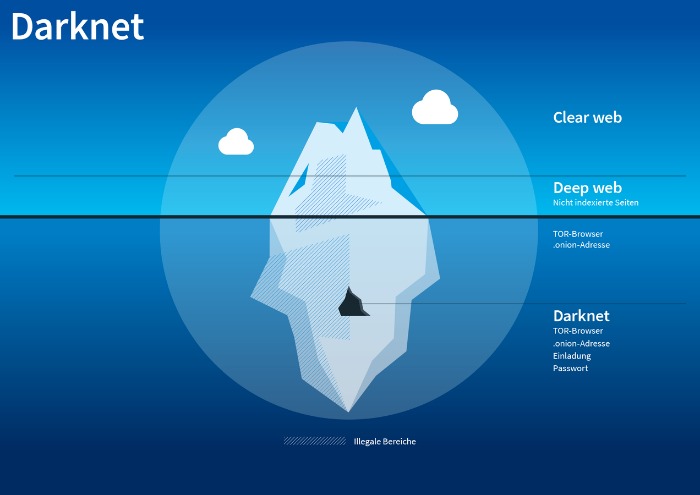
Cryptocurrencies, while offering enhanced privacy, also present significant risks. Users face vulnerabilities like market volatility, scams involving fake escrow services, compromised wallets, or theft through phishing schemes targeting crypto transactions. Furthermore, inexperienced users unfamiliar with secure cryptocurrency practices are particularly susceptible to these threats, risking the loss of their entire funds. The Dark Web—a hidden part of the internet accessible only through specialized software like Tor—has become increasingly significant as we enter 2025. Often portrayed as the internet’s shadowy underbelly, the Dark Web hosts marketplaces offering everything from privacy tools and digital currencies to more questionable, or outright illegal, products and services. Some vendors offer services to help people “clean” illegally obtained funds using cryptocurrency and fake transactions.
These platforms sell everything from drugs and fake IDs to weapons and hacking tools, resembling a digital black-market bazaar. Centralization issues arise not only from the control of watchtowers but also from the existence of multiple large nodes created by organizations, leading to a kind of dominance in the network. Some people believe that such a consequence of growth could undermine the decentralized nature of cryptocurrencies and potentially lead to problems such as censorship or transaction control. As the original idea of LN is made clear, this network enables near-instantaneous transactions with significantly lower fees than ordinary BTC transactions.
- To prevent the users from DDoS attacks, it provides personal marketplace domains to high-volume buyers and sellers.
- In 1993, “A Cypherpunk’s Manifesto” was published in the Cypherpunk mailing list.
- The integration of blockchain-based smart contracts is also becoming widespread, automating secure transactions and reducing the likelihood of fraud.
- There are also “fake” CoinJoins who leverage heuristics to confuse on-chain analysis into believing a transaction made by only one person is actually an elaborate CoinJoin.
- Markets prioritize Bitcoin for its liquidity, though some now accept Monero for enhanced privacy.
Is There A Future For Dark Web Marketplaces?
The idea for the Lightning Network was proposed by Joseph Poon and Thaddeus Dryja and subsequently implemented for Bitcoin. The Lightning Network aims to solve the scalability problems of blockchain networks by providing fast, cheap, and scalable off-chain transactions. At its core, the Lightning Network is a constellation of payment channels between two parties.
There’s always the possibility that the sender shoots himself in the foot. One way of accomplishing that is sending a 1 hop payment from a node with only one channel. If both the direct peer from the sender and the direct peer from the receiver are nodes controlled by the attacker, it knows who the sender, the receiver, and the amount of the payment being made. Compare the two snapshots above and see if you can identify how much Alice paid Bob and through which channels the payment passed through. Besides that, some heuristics can be applied by attackers to link payments to senders and receivers.

Payment Channels
Functionally, accessing DNMs and using them requires quite a few extra steps to protect the anonymity of the buyers, sellers, and server admins. To get into DNMs, you’ll likely have to figure out the basics of things like PGP encrypted messages and using the TOR browser. The .onion top-level domain (TLD) name is the dark web’s version of “.com” or “.net”. Unlike traditional TLDs, servers using the onion TLD are more difficult to locate.
Although a viable solution, Hash Time Locked Contracts (HTLC) would need to be programmed every time an Atomic Swap were to take place and can be difficult to understand for those not familiar with the technology. Atomic swaps are the exchange of different cryptocurrencies using a Hash Time Locked Contract (HTLC) without the use of centralized intermediaries. On the other hand, Bob has 100 litecoin, and wants to exchange them for 1 bitcoin. In a normal scenario and without using trusted third party, Alice would have to send Bob her 1 bitcoin and hope that Bob sends her the 100 litecoin instead of running off with her funds. That person goes to a hawaladar and states they want to send $100 to London.
What Is A Lightning Network Node?
Newer markets automate link verification using onion-cloaked TLS certificates, ensuring users connect only to authentic domains. This reduces exposure to exit scams or law enforcement honeypots, maintaining a safer shopping experience. Nexus Market and Abacus Market stand out in the 2025 darknet landscape for their streamlined, intuitive designs, making drug shopping efficient and accessible. Both platforms prioritize ease of navigation, with clean layouts, advanced search filters, and real-time inventory updates.
In developing countries, there is limited infrastructure in place to allow citizens reliable access to the internet, let alone afford subscription-based private access to the internet. Even amongst some of the largest economies, there is a great discrepancy in internet adoption between rural and urban areas. Once Alice has a sending potential of 0 bitcoin, she cannot add to this balance herself without closing the channel and creating a new one.

Case Study: Genesis Market And Telegram Broker Networks
Fees on the Lightning Network are minimal, often just a fraction of a cent, which opens the door for cost-effective microtransactions and encourages broader adoption for small, frequent payments. Users don’t need to open a direct channel with everyone they want to transact with. The Lightning Network can route payments through a series of existing channels using a network of nodes, ensuring fast and trustless delivery from sender to receiver—even if they aren’t directly connected. However, you can trace its roots to the development of technologies like the Tor network or Freenet.
This undermines Bitcoin’s goal of decentralization and could lead to single points of failure or influence if left unchecked. Physical merchants can integrate Lightning payments into their POS terminals, offering customers a fast and modern payment alternative without relying on cards or cash. To turn it on, just go to the “Settings” and then the “Tools” section of the NordVPN app and activate “Dark Web Monitoring.” In the end, it’s all about staying one step ahead.



