This makes it a great option for watching videos from streaming services that are available only in other regions of the world. Another reason you don’t want to use the Tor Browser for your daily web browsing is that it draws attention to you. The Tor Browser prevents your ISP from seeing what websites you’re visiting, but it does not prevent the ISP from seeing that you’re using Tor. As I mentioned previously, using the Tor Browser will slow down your browsing. Since your traffic goes through a series of relays, getting encrypted or decrypted along the way, things slow way down. This means Tor is a lousy option for streaming video, online gaming, or downloading files (torrenting).
Tor And The Dark Art Of Anonymity

These include the absence of support for XMR, Direct Pay options, and enforcement of PGP encryption. The MGM Grand is a darknet market of moderate size that has been in operation since April 10th 2021. Its recent surge in popularity can be attributed to the closure or inaccessibility of other markets.
Top 8 Darknet Markets
The FBI, DEA and international partners infiltrated the site during Operation Bayonet. On July 5, 2017, Thai police arrested founder Alexandre Cazes; a week later he was found dead in his Bangkok cell. Authorities seized AlphaBay’s servers and cryptocurrency wallets, replacing the homepage with a seizure banner and simultaneously taking over the rival Hansa Market to harvest user data. Operational security, or OPSEC, is the discipline that turns technical anonymity into real‑world protection.
More On Tor Onions
As you might expect, these websites sometimes host explicit, gory, harmful, and illegal content. In the internet’s darkest corners, a myriad of hidden websites cater to an array of needs and interests. From encrypted communication channels and hacking forums to illicit marketplaces, the dark web is a destination for millions of daily users.
Opennet connections are easier to use, but darknet connections provide more security against attackers on the network. The advantages of I2P are based on a much faster and more reliable network. Additionally, I2P doesn’t rely on hidden directories that serve as a resource for .onion domains. I2P can only be used to access hidden sites that are only available on the I2P network. Supreme Court will allow the FBI to search and seize any computer that’s using the Tor browser or VPN.

Why Is It Critical To Monitor Dark Web Marketplaces?
- All transactions are protected by multisig escrow and PGP encryption.
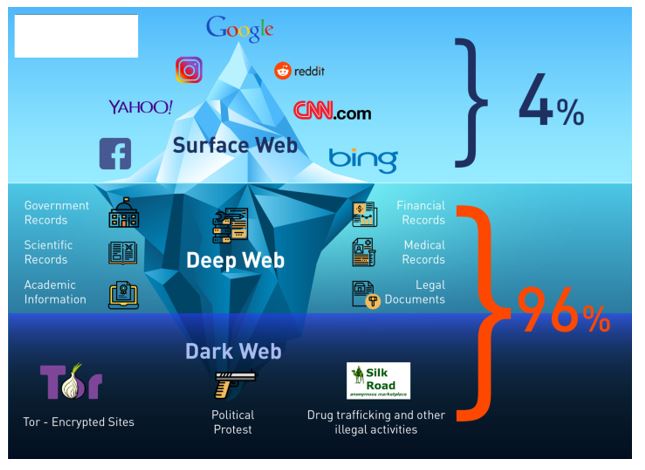
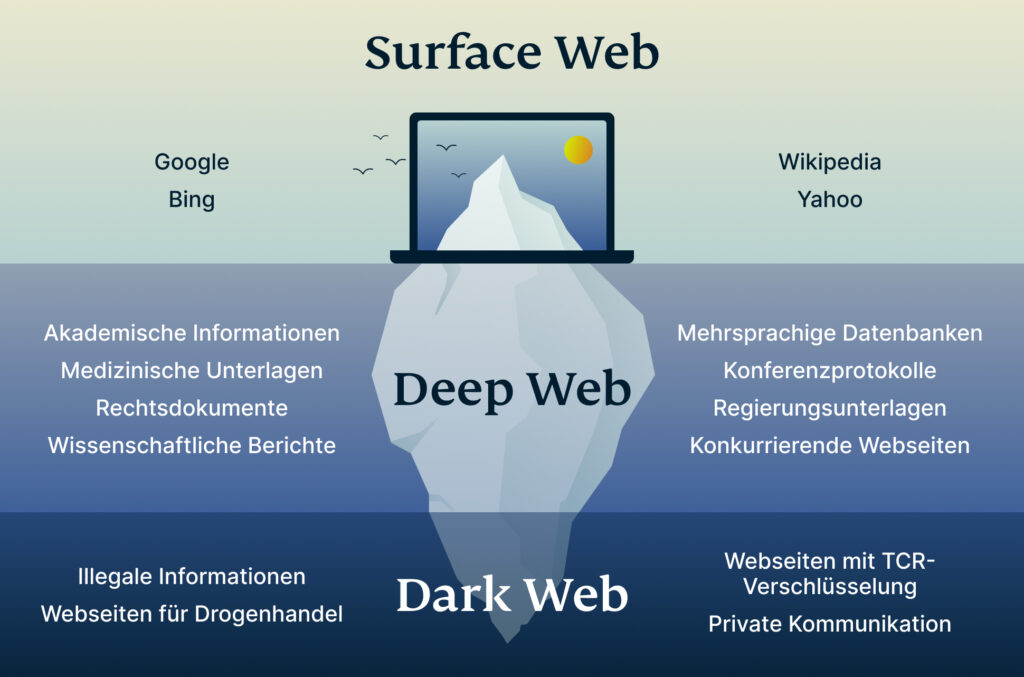
- Illegal marketplaces are merely a small fraction of what’s actually there.
- Not to mention that anonymity safeguards won’t protect you from other threats like hacking and malware.
- The concept of darknets emerged as a response to concerns about digital privacy and government surveillance.
- You’ll learn how it differs from the surface and deep webs, how Tor and similar networks maintain anonymity, and why some activities cross legal lines.
It is home to all sorts of disturbing content, given that the markets share content related to non-consensual recordings and child exploitation. Interestingly, the hackers don’t hide, but most of them even openly advertise what they offer on the darknet forums. Therefore, you can hire them to perform a task for you, from planting malware to hacking email accounts and even breaking into various social media accounts.
Structure Of The Internet: Surface Web, Deep Web, Dark Web
Darknet Marketplaces are underground black markets on the dark web! Shop for exclusive products in our marketplace, where privacy, security, and anonymity are always a top priority. Abacus hosts over 250+ active vendors offering a wide range of products, including drugs, digital goods, fraud tools, and counterfeit items. Step into the world of Archetyp, where anonymity reigns supreme. Archetyp Market is an online darknet marketplace, founded in late 2021.
Hacking And Cybercrime Sites
While an iOS version of the official Tor browser is not available, there are Tor-compatible browsers available in the App Store. Instead, you need to get the Tor browser to access the dark web. Make sure that when you download the Tor file, it’s from their official website. The dark web is a very popular platform for journalists, political bloggers and political news publishers, and in particular, those living in countries where censorship shields most of the internet. You can also find email messages, online bank statements, and much more information on the deep web – information that is usually private and inaccessible by the public on the surface web.
In terms of cybersecurity, the Dark Web is a place where Ransomware-as-a-Service kits and phishing methodologies are traded and leveraged daily. MGM Grand Market is making waves in the darknet marketplace with its sleek, minimalist design that enhances the user experience. Known for its commitment to ethical practices, especially its strong stance against certain prohibited content, MGM sets a benchmark for responsible operations in this arena. With its expanding vendor base, the market boasts an impressive selection of unique and exceptional items, offering more than the usual darknet fare.
- These tools leave no trace on your device and reduce your exposure even if something goes wrong.
- That all is for general internet activities, you can guess how crucial having a VPN is when you hop onto something like the dark web.
- Internet traffic first passes through the Tor Network, and then through the VPN.
- Bear in mind too, that your internet provider will be able to see you connecting to Tor nodes, even if it doesn’t know exactly what you’re doing.
- To access a dark web address, you must use a VPN and a suitable browser (it should be Tor).
- In fact, a recent judgment by the US Supreme Court denoted that simply using Tor was sufficient probable cause for law enforcement to search and seize any computer around the world.
Are Wi-Fi hosts and owners able to see what you’re doing online? Since their deadline wasn’t met for the closer of the sites a month later, the Impact team ascended to the dark web, where they started to publish the data. The child pornography site Playpen is one of the famous scenarios that resulted from the dark web. The site had only been up and running for about seven months, but surprisingly, it gained over 215,000 users.
For Example, In May 2021, authorities in Germany brought down Boystown, a child pornography network with more than 400,000 registered users. Several pedophile chat sites were also dismantled, and four people were detained, one of them a Paraguayan suspected of running the network. While some threats on the dark web are well-known, others may use its notorious reputation to trick users into paying large sums of money. Additionally, some users on the dark web may attempt phishing scams to steal personal information and extort victims.
Award-winning journalist Evan Ratliff spent nearly five years piecing together the uncommon story. The Goodreads community has responded well to the riveting account of a crime boss with thousands of positive reviews, and it’s no secret why the book tops our list. It offers much information to help you learn how the dark web works.
Commercial Services
The site operated under a cryptocurrency paradigm—Bitcoin, fundamentally revolutionizing online illicit trade. The darknet marketplace is home to a plethora of illegal and legal activities. However, the markets are dominated by things like illegal drugs, explicit content, pirated files, hacking services, and stolen personal information, among others. While there are legitimate products and services in the darknet markets, often, these markets deal with illicit goods and services like drugs, fake documents, and hacking services. Their presence can make you wonder why darknet markets and not just the regular online stores. If you’re using a browser like Tor and visiting .onion websites that aren’t accessible through regular search engines or browsers, you’re likely on the dark web.