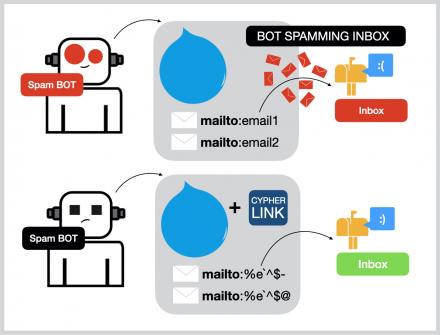
Cypher Market was a darknet market that emphasized external security (like anti-phishing measures) and user protection. It offered a relatively safe and secure environment for transactions, accepting both Bitcoin and Monero. While it was a newer market, it had a growing number of vendors and listings, covering various categories, including drugs, digital goods, and guides. Cypher Market had a clear set of rules prohibiting harmful content and activities. Generate secure links for recipients to decode messages using the same encryption key. Cypher ventures boldly into an array of product categories beyond the commonplace, spanning drugs, fraud, hacking, counterfeits, and defense/intelligence sectors, each thoroughly categorized.
Inadequate Input Validation
Cypher introduces you to the world of cryptography and graph database vulnerabilities, including various query techniques. Mastering Cypher involves deciphering encrypted messages, exploring directories, and exploiting server weaknesses. By delving into this realm, you’ll enhance your ability to identify and mitigate potential security threats. Get ready to unravel the mysteries of Cypher and enhance your cybersecurity expertise. As we look to the future, we’re excited to integrate cutting-edge augmented reality (AR) technology into our cypher url marketplace.
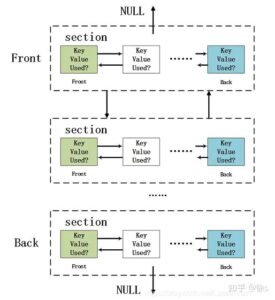
Read Query Structure
operator. Negative indexing in list slicing references elements from the end of the LIST; ..-1 excludes the last element, ..-2 excludes the last two elements, and so on. Closed dynamic union types allow for the testing of multiple types in the same predicate. The IS NOT NORMALIZED operator is used to check whether the given STRING value is not in the NFC Unicode normalization form. The IS NORMALIZED operator is used to check whether the given STRING value is in the NFC Unicode normalization form.
Tor Darknet Market
Given property uniqueness constraint on the name property for all Person nodes, the below query will match the pre-existing Person node with the name property Oliver Stone. Cypher prevents getting conflicting results from MERGE when using patterns that involve property uniqueness constraints.In this case, there must be at most one node that matches that pattern. Grant SHOW TRANSACTION privilege to list transactions by the specified users on home database to the specified roles. Grant SHOW TRANSACTION privilege to list transactions on all users on all databases to the specified role.
The toBooleanOrNull() function converts a STRING, INTEGER or BOOLEAN value to a BOOLEAN value.For any other input value, null will be returned. The function startNode() function returns the start NODE of a RELATIONSHIP. The nullIf() function returns null if the two given parameters are equivalent, otherwise it returns the value of the first parameter.
ON DATABASE Privileges
An MLP is a type of neural network composed of multiple layers of interconnected neurons, where each layer transforms the received input before passing it on to the next. This structure allows the program to detect subtle patterns in data, improve its accuracy, and adapt to different types of encryption more effectively. An encryption detector is a computer tool designed to recognize encryption/encoding from a text message.
Compliance Ready
Revoke DELETE privilege on all nodes and relationships in a specified graph from the specified role. Deny TRAVERSE privilege on all graphs and all nodes with the specified label and with a secret property not set to false to the specified role. List all users in Neo4j DBMS, returns only the default outputs (user, roles, passwordChangeRequired, suspended, and home). Alter the remote alias named remote-database-alias, set the username (user_name) and the password.
Cypher Market Details
- We read every piece of feedback, and take your input very seriously.
- We have to sacrifice the speed here with that loops becauseotherwise we would have to do operations on really large numbers.
- With our user-friendly interface and intuitive search tools, finding the perfect cypher market item has never been easier.
- The walkthrough for understanding how to identify vulnerabilities like command injection is key.
- The IS NORMALIZED operator is used to check whether the given STRING value is in the NFC Unicode normalization form.
Grant REMOVE PRIVILEGE privilege, allows the specified role to remove privileges for roles. Grant ALTER ALIAS privilege to alter aliases to the specified role. Deny SET PASSWORD privilege to alter a user password to the specified role.
Omg!Omg! Market (Ru)
- Powered by advanced algorithms and machine learning, our platform will analyze your browsing and purchasing history to provide you with personalized cypher darknet suggestions tailored to your unique preferences.
- Relationship pattern filtering on the ACTED_IN relationship type.
- These anonymous marketplaces—operating mainly on the Tor network—are now a primary threat vector for businesses and cybersecurity professionals.
- Use MATCH to find entities that must be present in the pattern.Use OPTIONAL MATCH to find entities that may not be present in the pattern.OPTIONAL MATCH returns null for empty rows.
- The asin() function returns the arcsine of a FLOAT in radians.
The asin() function returns the arcsine of a FLOAT in radians. The acos() function returns the arccosine of a FLOAT in radians. The log10() function returns the common logarithm (base 10) of a number.
Create a range index with the name index_name on nodes with label Person and property name. The point() WGS 84 3D function returns a 3D POINT in the WGS 84 CRS corresponding to the given coordinate values. The point() WGS 84 2D function returns a 2D POINT in the WGS 84 CRS corresponding to the given coordinate values.
Can I Decode Messages Without Knowing The Original Encryption Method?

For beginners delving into Cypher on HackTheBox, essential tools and techniques are pivotal. Utilize tools like gobuster for directory enumeration and Chisel for tunnelling connections. Employ Python scripts and pip for automation and creating payloads within an archive of folders. Understanding basic Linux commands is fundamental for navigating systems. To mitigate risks, regularly scan for vulnerabilities utilizing tools like John the Ripper and exploit them effectively.
Welcome to our comprehensive marketplace, where you’ll find the best cypher link products from the top online retailers. Discover a wide range of high-quality cypher onion items, all handpicked to meet your needs. Our anonymous aggregator service ensures you get the best deals, with the convenience of a single platform. Experience the ultimate shopping experience and unlock the secrets of the most successful cypher url marketplace.