In the world of onion sites, there are various types of services available. Some are designed for privacy-focused communication, while others provide marketplaces or forums for specific communities. Due to the unique nature of the Tor network, these best onion sites often thrive in anonymity, providing users with accessible services that prioritize privacy. When you access an onion site, your connection is first routed through a series of these nodes, which are randomly selected. This not only anonymizes your IP address but also encrypts your data multiple times. Each node decrypts its layer of encryption, revealing the next destination node until the traffic reaches the final onion service.

Is ChatGPT Ready To Take On The Mantle Of A Search Engine?
Using DuckDuckGo over Tor will also let you see onion sites and normal pages in your search results. The Tor Browser can take you to all kinds of questionable, dangerous, and potentially illegal content. That’s why knowing which dark web websites are safe to visit is vital. The dark web is mainly made up of the onion sites on the Tor network and can only be accessed via Tor and the Tor Browser.
Dark Web Links: The Best onion And Tor Sites In 2025
However if your computer, browser, or you yourself give away personal information you can be identified. Download free Avast Secure Browser to get automatic incognito browsing, block web tracking, and protect your personal data. Install free Avast Secure Browser to get automatic incognito browsing, block web tracking, and protect your personal data. Make sure you have a reputable antivirus running on all your devices.
Act 1: Where The Onion Service Sets Up Its Introduction Points
Borderless news reporting and uncensored media are among the most important and practical uses for the dark web. Bypassing firewalls and other forms of geo-blocking helps people to access news websites and social media they normally wouldn’t be able to — and do so with less fear of recrimination. Torch is the oldest and largest .onion search engine with more than 1 million .onion sites indexed. Just bear in mind that many of those will be out of date, and using this index will require a lot of discretion, due to its size. In addition, Ahmia and Haystack make every effort to filter out and blacklist sites known to contain harmful, abusive, or illegal content. This makes them a safer (though still not foolproof) option for searching the Dark Web.
What Are Onion Sites? A Guide To Accessing The Dark Web – Trusted Insights From TorConnect
Journalists use two USB flash drives and two personal computers to access SecureDrop data. The first personal computer accesses SecureDrop via the Tor network, the journalist uses the first flash drive to download encrypted data from the Internet. The second personal computer does not connect to the Internet, and is wiped during each reboot. The first and second flash drives are inserted into the second personal computer, and the material becomes available to the journalist. That portion of the web which cannot be easily reached from the public Internet, and usually requires specialized software to access. Examples of the dark web are the Tor network and hidden services (.onion), the I2P network and its eepsites (.i2p), and the RetroShare network.
- At $9.99/month, you can migrate to a premium plan with 500 GB storage and unlimited messages.
- The site also uses strong encryption to protect against cyberattackers, such as anti-DDoS protection.
- Due to the unique nature of the Tor network, these best onion sites often thrive in anonymity, providing users with accessible services that prioritize privacy.
- The tool is simple to install, fast to learn, and gets you started immediately.
- Secondly, after the order is submitted, proving ownership over each domain is required.
- KeyBase combines encrypted messaging with secure file sharing and identity verification.
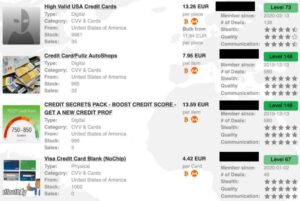
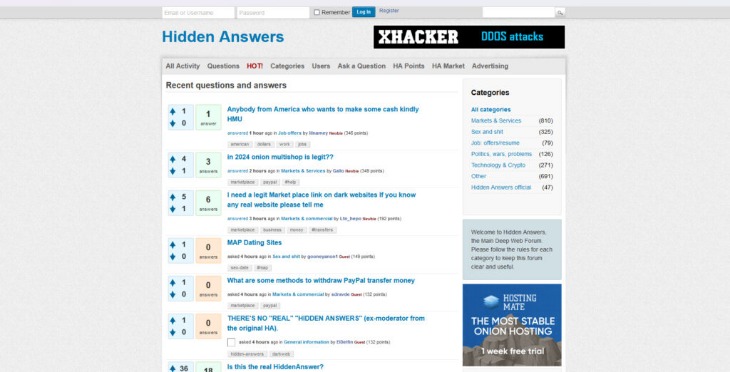
Trusted Directories And Forums (stay Away From Hidden Wiki)
And inside the descriptor, there are the introduction points that allow the client to introduce themselves to SecureDrop’s Onion Service. All the previous steps were just set up for the Onion Service so that it’s reachable by clients.Now let’s fast-forward to the point where an actual client wants to visit the service. This looks weird and random because it’s the identity public key of the Onion Service.That’s one of the reasons we can achieve the security properties above. Dark Web can be a useful place if you know how to safely navigate it. Protect your business with end-to-end encryption and compliance-ready security. I want to know what this really mean and what is the difference between a normal link and Tor link.
How Do I Browse Onion Sites Safely?
- Whistleblower Aid is a complimentary service to SecureDrop, which protects those brave enough to expose wrongdoings.
- However, note that the site only uses non-sensitive and public data for the metrics.
- But users should always be cautious and avoid clicking unfamiliar or untrusted links to steer clear of scams or malware.
- Users must implement additional tools and practices to ensure comprehensive protection while browsing onion sites.
- Some businesses utilize onion sites as a means to offer services or products discreetly.
The official Tails OS documentation is also accessible through an .onion mirror, offering users critical setup and usage guides directly over Tor. This is especially valuable for people in censorship-heavy regions or under surveillance. These docs walk users through secure browsing, file storage, and messaging practices, all while maintaining the integrity of anonymous operating environments. ZeroBin is a paste tool that allows you to publish and share encrypted text anonymously.
How To Open Facebook App Links In Android’s Chrome Or Edge Browser
The main argument they present is that end users wouldn’t know how to go in and enable Javascript on sites that they require it on. The other concern with disabling Javascript is that it is possible to potentially fingerprint your specific ruleset of whitelisted domains for Javascript. Tor Browser is currently available for Windows, Mac, Linux, and Android — you can download it from the official Tor website. After installation, you can use Tor to access the public internet as well as .onion websites. Still, Tor and the dark web have a stigma attached due to the undercurrent of illegal activities.
The encryption provided by the Tor network allows users to share sensitive information without interception. Once you have installed the Tor Browser, you can begin exploring various onion sites. It is essential to use reliable directories or resources that list the best onion sites to avoid connecting to potentially harmful or illegal domains. Remember, not all content on onion sites adheres to legitimate standards, so practicing caution is paramount. This website used to host over 7,000 onion sites, giving users access to many dark web links.
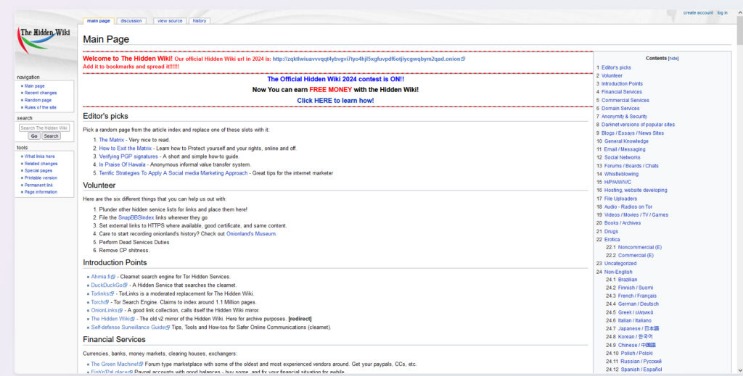
The Hidden Wiki is a gateway to these deep web resources, offering links to .onion sites that cannot be found via Google or other surface web search engines. Thus, users who want to explore hidden, uncensored, or private content often rely on tools like the Hidden Wiki because it provides structured access to resources beyond Google’s reach. Another critical advantage of the Hidden Wiki lies in its resistance to censorship. This makes it an essential resource for users living under oppressive regimes or in countries with strict internet controls. The Hidden Wiki empowers people to access alternative viewpoints, engage in uncensored discussions, and exercise freedom of information that surface web search engines cannot guarantee. Once you have the Tor Browser installed and optionally connected to a VPN, you can access the Hidden Wiki by entering its .onion URL directly into the browser’s address bar.
Facebook’s official dark web version helps users access the platform in countries where it’s blocked. During testing, I confirmed it provides the same functionality as the regular site while adding Tor’s privacy benefits. The interface works smoothly, but it usually loads slower due to Tor routing. Adamant offers blockchain-based secure messaging without needing phone numbers or email addresses. The platform stood out during my testing for its commitment to anonymity — all messages are fully encrypted and stored on a decentralized network. It’s particularly useful for sensitive communications that need to remain private.
How To Access The Dark Web
It uses public key cryptography to ensure the chats remain anonymous to everyone except the participants. Using Forest VPN is essential for protecting your privacy while browsing these sites. It encrypts your connection, ensuring anonymity as you explore the dark web. Luckily, Facebook has a dark web version that allows people to access the online network even in countries that prohibit it.
The use of the dark web raises suspicion as it shows there is something you want to do privately. Nowadays, many people use the Tor browser to surf the public internet and navigate the deeper parts anonymously. The system is designed to provide enhanced security and privacy features. Its key features include kernel hardening, application firewall, package security, filesystem encryption, meta-proxy encryption, and binary integrity. The only difference is that it passes your traffic through random nodes before reaching the destination.