In 2019, there were approximately 8,400 active sites on the dark web, selling thousands of products and services daily. As of 2020, nearly 57% of the dark web was estimated to contain illegal content, including violence and extremist platforms. And, of course, think twice before sharing too much personal details online. That all is for general internet activities, you can guess how crucial having a VPN is when you hop onto something like the dark web. Sometimes, you might be hacked by using weak passwords or even just connecting to unsecured Wi-Fi on public networks. And in a world where almost everything we do is online, taking your digital privacy seriously is more important than ever.
What Are Onion Sites And Dark Web Websites?
What current policing strategies neglect is that dark web markets are not isolated to the storefronts that are the popular target of crackdowns. These are communities stretched across dark and surface web forums which develop shared tutorials and help one another adapt to any new changes. These closures bind users together and foster a shared resilience and collective experience in navigating these environments.

The Birth And Rise Of The Silk Road
It’s incredibly common for darknet marketplaces to be held for ransom by hackers or attackers. These attacks usually involve DDOSing (overloading) the service and demanding a crypto payment from the site admins to stop the attack. Once the website is coded, the policies created, the admins ready, and the hosting secured, the site goes live on the TOR network. Buyers won’t come to the site if there’s nothing to buy, and sellers won’t come to the site if there’s no one to buy their products. Server admins will have to either make special agreements to get initial sellers on board, or supply products themselves to get things started.
Dark Web Market & Threat Predictions For 2025
We deliver contextualized, actionable intelligence through our dedicated platform or API integration, ensuring that you can respond effectively to darknet threats. While some of this growth may be attributed to the reposting or combining of older leaks, cybercriminals are clearly interested in distributing leaked data – whether new, old, or even fake. Consequently, in 2025, we are likely to witness not only a rise in company data hacks and leaks through contractors, but also an overall increase in data breaches.
Fortify Your Mobile Protection: Building Customer Trust With Advanced Security
- Implementing strong authentication protocols, such as multi-factor authentication (MFA), significantly reduces the risk of unauthorized access.
- While some of this growth may be attributed to the reposting or combining of older leaks, cybercriminals are clearly interested in distributing leaked data – whether new, old, or even fake.
- The majority of established and popular services have maintained their presence in the market, with little change in the competitive landscape.
- Early participants may see some profit, but that money usually comes from new victims, not actual earnings.
Despite its name, the marketplace operates primarily in English and serves a global audience. It has gained a reputation for being a reliable source of high-quality data for cybercriminals. Based on our observations from analysis on dark web data using Lunar, we’ve identified the top 7 marketplaces on the dark web in 2025. We developed Lunar to monitor the deep and dark web, including dark web marketplace sites. By supplying stolen data, these dark web links fuel many online scams and identity theft operations, playing a critical role in the darker aspects of the internet.
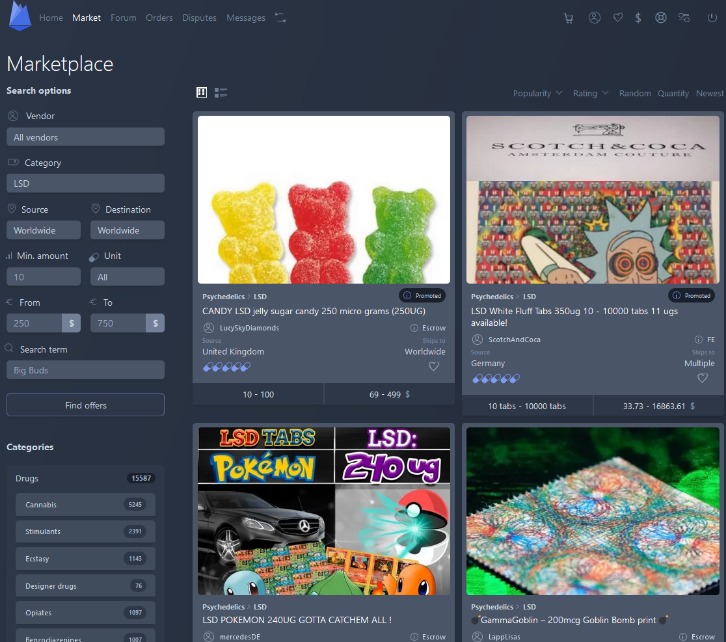
Darknet Markets Explained: Navigating The Hidden Web

In a world where data is a valuable asset and cyber threats evolve rapidly, understanding how dark web marketplaces operate is essential. While the anonymity they offer can embolden criminals, staying informed and taking preventive actions are key to remaining secure. To analyse the connectivity of the whole ecosystem, i.e., how markets are connected with each other, we consider sellers and buyers that are simultaneously active on multiple platforms. In particular, multihomers that are sellers in multiple markets are multisellers, and similarly for buyers we have the multibuyers. Specifically, to be classified as a multiseller, a user must be classified as a seller in at least two markets simultaneously.
Biggest Darknet Players In 2025
The seized drugs included 141 pounds of fentanyl or fentanyl-laced narcotics, more than 569 pounds of amphetamines, 95 pounds of cocaine, 95 pounds of MDMA and 22 pounds of LSD and ecstasy pills, authorities said. Russian private military contractor Wagner is busy boosting its brand as its fighters try to subdue Ukraine, trading secrecy for war propaganda movies. The Malware-as-a-Service model is expected to expand as it lowers the barrier for entry into cybercrime.
It ensures the buyer’s identity is kept hidden and accepts payments through cryptocurrencies, including Bitcoin, Litecoin, Ethereum, and Monero. Freshtools was established in 2019 and offers various stolen credentials, accounts, and host protocols like RDP. It is considered a go-to site for malware purchasing, providing keyloggers, trojans, and other Malware as a Service products. Due to its extensive inventory and reputation for reliability, Brian’s Club has maintained a significant presence on the dark web.
The Magical Comeback: Kaspersky And BIZONE Report New PipeMagic Activity In Saudi Arabia And Brazil
Data breaches also present a critical challenge, as stolen credentials allow attackers to infiltrate systems and extract sensitive information, including customer data and trade secrets. These breaches can result in regulatory penalties for failing to comply with frameworks such as GDPR or HIPAA. For example, non-compliance can result in fines of up to 4% of an organization’s global annual revenue.
How KELA Cyber Supports You In Darknet Monitoring And Risk Mitigation
They mix and transfer funds through various privacy wallets and escrow services to hide the original source and make the illicit transactions harder to trace. Torzon Market showed up on the dark web in September 2022, and it’s been growing steadily ever since. These days, it lists over 11,600 illegal items, including hard drugs, hacking tools, and all kinds of cybercrime services. Looking ahead, the darknet drug trade is expected to grow further, driven by advancements in blockchain technology and increased adoption of privacy-focused cryptocurrencies like Monero.
The darknet drug market continues to grow, with 2025 projections indicating expanded availability and improved user experience. Darknet magazines and forums provide updates on new markets, onion addresses, and URLs, facilitating seamless transactions. Cryptomarkets on the darknet remain a key resource for those seeking privacy and efficiency in online trade. Dark web marketplaces are online platforms operating within the dark web, where individuals trade illicit goods and services while preserving their anonymity. Unlike traditional e-commerce websites, these marketplaces rely on encrypted networks like Tor (The Onion Router) and cryptocurrencies such as Bitcoin to conceal user identities and transactions. This unique infrastructure fosters an environment for illegal commerce, posing significant cybersecurity risks for businesses.

It is a wallet-based shop, meaning you must first deposit bitcoins into your wallet before purchasing any goods and services. The marketplace is much more organized, which makes it easy to use and navigate. This guide outlines different ways of safely accessing dark web stores and the list of reliable dark web marketplaces you can consider visiting in 2025 for research and monitoring purposes.
Many people install a VPN as well, but then you’re putting your trust in an additional third party to not track your activities or report them to anyone else. Exploring the dark web can be eye-opening, but it’s also risky without the right protection. While the Tor browser boosts privacy, pairing it with a VPN adds a critical layer of security. On the dark web, traffic is routed through multiple server nodes that don’t log activity, obscuring the user’s origin and enabling anonymous communication. Usually these products are sent to the buyer by post and money transferred to the seller through the escrow system. Monero’s ring signatures, stealth addresses, and RingCT ensure untraceable trades.