
If someone has the market’s code to the infrastructure, no matter how much effort law enforcement puts in, it will keep coming back on another server or can be built again with the same branding. What’s more concerning is that most of the time, we don’t know about these flaws, and by the time we try to fix them, we come to know it’s too late. Like ransomware, criminals can buy software and inject your devices with viruses. With it, they can spy on people, steal their sensitive data, or secretly control their devices. These software are also capable of launching DDoS attacks and phishing campaigns.
Unlike Bitcoin and other cryptocurrencies that leave traceable transaction records on public blockchains, Monero offers genuine privacy protection through advanced cryptographic techniques. You can use a dark web scan tool to tell if your data has landed on the dark web. The tool scans the dark web marketplaces and forums for signs of compromised personal credentials. In response, darknet market vendors are increasingly shifting their financial activity toward decentralized platforms. You can buy credit card numbers, all manner of drugs, guns, counterfeit money, stolen subscription credentials, hacked Netflix accounts and software that helps you break into other people’s computers.
Tweak Tor Browser Settings
The security level is set to ‘Standard’ by default, but you can change it to the ‘safest’ and enjoy more security while accessing the dark web. Besides this, it supports wallet-less transactions and accepts payments through Bitcoins, Litecoin, Monero, and Zcash. However, you must wait some time to reassess this marketplace because it’s been shut down.
Top Darknet Markets 2025
On the other hand, some people might visit Darknet Markets for lawful purposes such as research, journalistic work, or simply to explore online communities. It’s essential to know the local laws regarding online activities, and be cautious when using these platforms to avoid any potential issues. Hackers spend a lot of time on the dark web, and it’s not too difficult to get access to hacking tools and data leaks in this part of the internet.
- Despite minor accessibility inconveniences, these strengths have solidified its position among the top dark-web marketplaces in 2025.
- In fact, WeTheNorth is more of a private club than an open market – something its operators want.
- These unique URLs, accessible only through the Tor network, provide an additional layer of anonymity by masking user identities and locations.
- These markets leverage advanced encryption technologies, such as Tor and PGP, to ensure that transactions remain private and secure.
- In 2025, the darknet drug trade continues to evolve, with markets expanding their offerings to include a wider range of products.
Top Darknet Markets
The use of digital signatures can also help verify the authenticity of users and transactions. These markets have also improved their user interfaces, making navigation and product discovery more intuitive. The use of Tor and other privacy-focused tools ensures that users can access these platforms without compromising their anonymity.
The email service is available both on the surface and on the dark web. Many social media platforms keep their presence on the dark web, and it is no surprise that Facebook has a .onion portal. Facebook’s dark web version allows users to access the site where it is banned or restricted.
Loss Of Anonymity
- Despite growing crackdowns from law enforcement agencies, the dark web remains a hotbed of criminal activity, offering everything from drugs to stolen data.
- You can quickly get into trouble for acting illegally, such as infringing on other people’s safety and freedom.
- These platforms leverage advanced encryption technologies and decentralized systems to ensure that transactions remain private and secure.
- It uses the Tor network because it is a popular network that helps to circumvent censorship and online surveillance.
- For example, you shouldn’t pirate copyrighted material, engage in terrorism, or share illegal pornography.
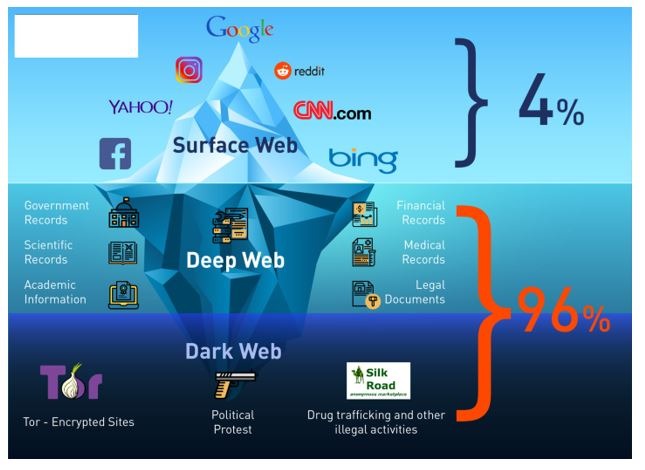
There are some things that you can’t find on the surface internet but are available in the darknet markets. Therefore, it’s almost impossible for authorities to track those who run the darknet markets or even their locations. Yes, the darknet still exists and continues to operate through networks like Tor, I2P, and Freenet. While law enforcement regularly shuts down illegal marketplaces, the underlying infrastructure remains functional.
Torzon Market

This option is ideal for digital products, domestic shipping, and transactions with established, high-reputation vendors. Our escrow system ensures that both buyers and vendors are protected throughout the entire transaction process. The market has built trust among users as it brings vendor reviews from different places and then verifies them with PGP signatures – that way, the buyers feel confident.
Furthermore, it’s critical to understand that Whonix is not a stand-alone browser. It is a component of Whonix, an operating system that functions as a whole inside a virtual computer. It includes all the essential productivity software, including MS Word and an email client. Another essential security feature is that all incoming and outgoing data from the app is encrypted, including any private and public keys involved. Some of the deep web sites do not use standard top-level domains (TLD) such as .gov, .com, .net, etc.
Secure Your Cryptocurrency Transactions
Dive into its etched saga, wield its cryptic machinery, or breach its threshold. Whether you chase shadows or stake your claim, this crypto nexus pulses with unseen power. This command monitors Tor relay traffic on ports 9001 and 9030, commonly used by the Tor network.
Similar Sites
The largest underground financial market exists for currencies in nations with strict currency controls. While most people may shun an underground market because they consider it sleazy, there may be rare occasions when they have no choice but to turn to this necessary evil. Most likely, the native account on your device has full admin permissions by default.

Experience The World’s Most Advanced Cybersecurity Platform
It’s been a constant back-and-forth between cybercriminals and law enforcement, with each new site trying to be smarter and more secure than the last. The second category consists of data stores, which specialize in stolen information. Today’s cybercriminals spread their activities across multiple platforms, making them harder to track and shut down. If you want more peace of mind, NordVPN has a dark web monitoring tool you can consider using.

Bear in mind too that laws about freedom of speech and censorship vary from country to country, which is part of the reason the dark web exists in the first place. Cybersecurity has to also cover everything physically on your computer too—which law enforcement or government authorities might have the right to seize if they come calling. If you want to be untraceable and undetectable, connecting to the dark web via the Tor browser is a major step towards that, but not the only step you’ll need. To get on the dark web, you need a browser built for the job, and the best in the business is Tor. Tor is a browser engineered for extra security and privacy, and can be used to navigate the normal, surface web as well as the dark web. It blocks trackers, prevents user fingerprinting, encrypts data, and reroutes your browsing so no one can see where in the world you are.



