Insurance is a safety net to protect you and your family’s financial well-being in the case of an unexpected loss. It is a legal arrangement that guarantees support in the event of a covered accident or incident. The dark web consists of websites that use encrypted .onion domains, which require specific software and protocols to access.
Sony Does Not Want People Buying Bootleg Benson Boone Merch And They’re Going To Court Over It
I strongly recommend surfing on the dark web using virtual machine software instead of your locally installed Windows. Because it’s easier to contain malware in a virtual environment, which can be fully controlled. There’s no broad consensus on dark web safety, but you at least need to use Tor and VPN together.
A Primer On The Dark Web And The Different Types Of Internet?
This VPN has various features that keep you safe on and off the dark web. It uses 256-bit AES encryption for maximum data protection, has a no-logs policy, and protects against IPv6, DNS, and WebRTC leaks. It prevents your IP address from ever falling into the wrong hands in the depths of the internet via “Network Lock,” its kill switch available across all major platforms. Already a household name in the VPN market, its developers keep upgrading it with new features to keep it ahead of its competitors. One of the most trusted VPNs for the deep web and the dark web security, it effectively blocks malware, ads, web trackers, and other online threats.
- Moreoever, the servers are owned by the organizations that use the service.
- Create anonymous profiles for any website you register with on the dark web.
- Right now, you can use many cryptocurrency .onion sites to buy or sell all types of cryptocurrencies.
- Launched in the early 2010s, Archive Today’s primary mission is to combat the transient nature of the internet, where web content can change, disappear, or be altered without notice.
- In Calgary, police say it’s difficult to pinpoint how many drug users are flocking to the dark net — and how much they’re buying — because the markets change constantly.
- Here’s a quick tutorial on how to safely access the dark web and tips on how to use it.
What Is The Surface Web?
It doesn’t censor out any content, so you’ll have free access to more than 400,000 indexed pages. I like that you can ask the search engine to match all of your search words for exact results, or only some of them for broader search results. Sure, it’s not as secure as the clear web version, but it’s there and totally legal to use. Hidden Facebook is hardly the only social media client on the dark web. Privacy and anonymity are the dark web’s hallmarks, thanks to a network of servers that hide users’ identities and locations.

This dark web monitoring will help you track illicit activities and minimize the risks of cyber-attacks. Additionally, despite the Dark Web’s security and anonymity features, law enforcement agencies use advanced technologies to track users engaged in illegal activities. If you do accidentally stumble upon illegal content like child porn on the Dark Web, your best recourse is to immediately leave the site and report it to the police. In the deep net, web crawlers are blocked from accessing web pages to gather information for indexing, so the content remains hidden.
Real-Time CTI News
This is because Tor traffic is usually unencrypted when it passes through the exit node. However, using the dark web for illegal activity can be a criminal offense. After all, some websites on the deep web are like those on the open internet, except that they are hidden behind a paywall or protected via passwords to limit access. While other dark web browsers (like Brave) can support onion links, the Tor Browser is highly recommended because it’s preconfigured with security and anonymity features optimized for the dark web. The platform includes a broad mix of content, from forums and marketplaces to privacy-focused resources, though it doesn’t filter out illegal sites, so caution is necessary.
- This does not protect you from malicious exit nodes, as your internet traffic is unencrypted by the time it reaches its destination.
- Liam says he takes drugs to medicate the effects of childhood trauma (he was beaten by one of his parents, he says) but that he’s seeking help.
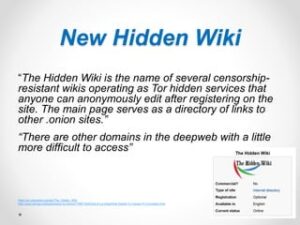
- The Hidden Wiki categorizes links under several headings, making it easier for users to find what they’re looking for.
- The RCMP say they have a national investigative strategy to combat the mail order drug trade in partnership with Canada Post, Health Canada, CBSA and other law enforcement agencies.
- However, using the dark web for illegal activity can be a criminal offense.
PrivateAlps
It is crucial to remember that using Tor is not illegal, but engaging in cyber-terrorism or other unlawful activities through it is. However, the Dark web is a portion of the deep web that can only be acquired through special tools. Still, primarily, this is used as a benefit for hackers and attackers or other illegal things like drug businesses. If you are dealing with others on dark web marketplaces, use pseudonyms or other accounts to protect your identity.
Dark Web Search Engines
As many as 70.79% of users claim to use the Tor browser for anonymity, 62.28% said they use it for additional security, and 27.07% used it out of curiosity about the dark web. If you are using sites like Spokeo to look up coworkers or neighbors, then yes, it’s probably not an activity you want to engage in. If you are using it to look at library inventory, old newspapers, or to find scholarly journals, then it’s completely fine. DuckDuckGo focuses heavily on privacy and not tracking users, all while allowing you to search the Surface Web.
As a result, you can be exposed to different malware types, including botnets, ransomware, keyloggers, and phishing. Unfortunately, others are fake and fraudulent websites that exploit the reputation of the dark web to con people. Moreover, malicious actors can attempt phishing scams to steal your data and identity for extortion.
Is It Safe To Visit The Dark Web On An IOS Or Android Device?
A bridge creates an obfuscated relay on the Tor network that is not listed in the main directory. That means that even if an ISP is monitoring all of the known Tor relays, they may not be able to block all of the obfuscated bridges. One of the major advantages of using Tor in overly-restrictive countries is that it keeps your online travels private. Unfortunately, some oppressive regimes have figured out a way to block Tor traffic. Using a VPN in conjunction with the Tor Browser is an excellent way to keep your online travels secure and private. A VPN’s ability to hide your Tor usage from your ISP and from government authorities makes for a valuable addition to your online privacy arsenal.
The Hidden Wiki

Virtual Private Networks (VPNs) keep you safe when surfing the internet in various ways. The most obvious way is by hiding your computer’s IP address and assigning you a new one, usually a different region. Antivirus software protects you from malware, spyware, and other computer viruses rampant throughout the deep and dark web. When you activate the software, it actively scans any files your device saves from the internet before they get saved onto your phone. The average person doesn’t share their private life with just anyone; they let specific people know about it when the information is needed.
Cybersecurity experts should pay close attention to these trends, as they often indicate emerging threats and profit-generating tactics among the cybercriminal forums. Active for a decade since 2014, it is a widely used credit card shop used to source stolen credit card information such as dumps, CVVs, Wholesale Accounts. It maintains a very strict level of user verification and integration with an official Telegram account to provide real-time updates to users.