Scammers on darknet markets claim to offer legit tools or services, but instead provide you with malicious software that can infect your device. However, if we’re being honest, the majority of activity on darknet markets involves illegal or heavily regulated items. A 2020 study found that almost 57% of sites on the Tor network hosted some form of illegal content. These markets are dangerous anyway and shouldn’t be accessed even if they’ve onion addresses. It safeguards the user’s online activities and identity by encrypting internet traffic and directing it through a series of TOR servers. While the TOR browser is frequently employed to access the dark web, it can also be used to browse the regular web more securely and privately.
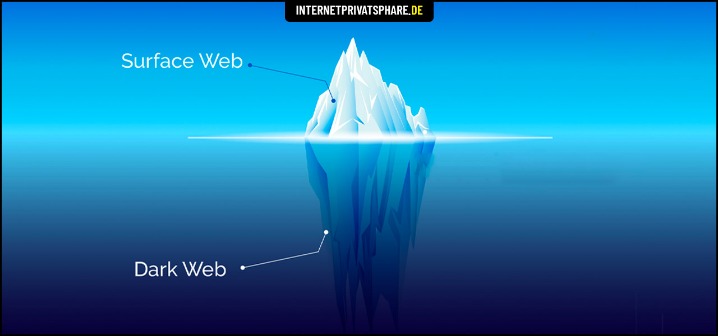
Hacker services against banks and other financial institutions are offered there. As you are now familiar with the three different sections within the entire world wide web, let’s take a closer look at how you can access the dark web anonymously. We’ve also previously mentioned the “dark users” that use the dark web for illegal reasons, but the less said about them, the better. Those who access the dark web do so via the Tor (The Onion Router) browser.
- Since the ISP can’t detect you’re accessing dark web URLs, it won’t trigger any alarms about your online activity.
- Given the amount of illegal and unsettling content on the dark web, there is always a risk that you might encounter something that could disturb you.
- The BBC news website has a special .onion site, which you need to access via the dark web.
- Even without the code, you can visit the security section to get tips on improving your daily life privacy.
- As we navigate these digital waters, Forest VPN stands as a steadfast ally, ensuring our journeys are private and protected.
Secure Your Connection
Pirate Bay, a BitTorrent site that law enforcement officials have repeatedly shut down, is alive and well there. Dark web websites look pretty much like any other site, but there are important differences. Instead of ending in .com or .co, dark web websites end in .onion.
The Hidden Wiki
It operates in both French and English and has built a reputation for ease-of-use. Known for its publicity stunt releasing millions of stolen card details for free, BidenCash specializes in credit card fraud and identity theft. It is one of the most controversial platforms, active since 2022. If you want to access the dark web, your first step toward a more private experience should be to secure your internet connection and data with a reliable VPN.
Ethical And Legal Boundaries In Monitoring Darknet Marketplaces

Now, that is not to say illegal behavior is completely beyond detection. Now that you understand what the dark web is all about, you might wonder why other people do things on it. Darknet marketplaces like to exist on the dark web because it offers a service that the regular internet, or more accurately, the “surface web,” does not. Instead, download Tor, the most secure and user-friendly option for accessing .onion sites. Despite some skepticism about its origins and privacy due to its military development, Tor remains the preferred choice for safe dark web navigation. The deep web is just the part of the internet you can’t find with a search engine.
About TorConnect
There’s no guarantee that placing an order with any DNM vendor will be safe or shipped. Functionally, accessing DNMs and using them requires quite a few extra steps to protect the anonymity of the buyers, sellers, and server admins. To get into DNMs, you’ll likely have to figure out the basics of things like PGP encrypted messages and using the TOR browser.
Established in 2022, Torzon market is one of the biggest and most diverse marketplaces on the dark web. It is considered very secure thanks to strict user validations and transparent payment and vendor review procedures. This is one of the most valuable resources available on the dark web.
Torch – Oldest Tor Search Engine
You can easily find what you are looking for, even links to hidden dark web rooms. With its nifty “conjoin” feature, users can combine different coins in one transaction, covering the user’s tracks and maintaining their anonymity. The wallet is user-friendly and provides robust security, making it one of the best crypto wallets on the dark web. Finally, Wasabi Wallet is non-custodial, meaning you alone can access the encryption keys. Another standout feature is that the servers can’t see what you type, copy, paste, or send. To increase the security level, add password protection and determine the expiration time for messages.
You must review the site’s descriptions before you click to open them. If we need a website to get links to other hidden sites, we will choose Hidden Wiki. But if you are thinking you can find links to the deepest part of the dark web using this site, it’s not that simple.
Is Using A VPN Necessary While Accessing The Dark Web?
The Darknet is a subset of the Internet operating over encrypted, anonymous overlay networks that require special software like Tor, Freenet, or I2P. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Individual sites on the dark web look much like they do on the regular web, though a lot of them are a bit more rough around the edges.
Buying Bitcoin (BTC)
However, this feature is only available on iOS, Android, and Windows. A top-of-the-line VPN network that ensures maximum security while accessing dark sites online. ActiveX and Java frameworks are susceptible to being exploited by hackers.

If a breach is detected, BreachGuard will notify you right away and help you take the steps you need to secure your data immediately. While some reports of dark web murder-to-order are overblown, it is possible to commission acts of cybercrime on the dark web. These range from phishing campaigns to DDoS (distributed denial of service) attacks, which can take down entire servers and websites. Dark web domains tend to be inconsistent — new ones pop up and others disappear, which makes sense if they offer questionable or illegal goods and services.
- Many other DNMs have sprung up since selling drugs, stolen merchandise, stolen information, and more.
- It is also used by whistle-blowers, journalists, and other individuals who are not involved in illegal activity but need to protect their communications and identities.
- They even have a Telegram channel to provide their clients with live updates.
- So, you’ll be happy to know there are several easy ways to delete a page in Word, including both blank pages and those you simply no longer need.
- However, it is estimated that the dark web makes up only a small fraction of the overall internet, likely less than 0.01% of the total content.
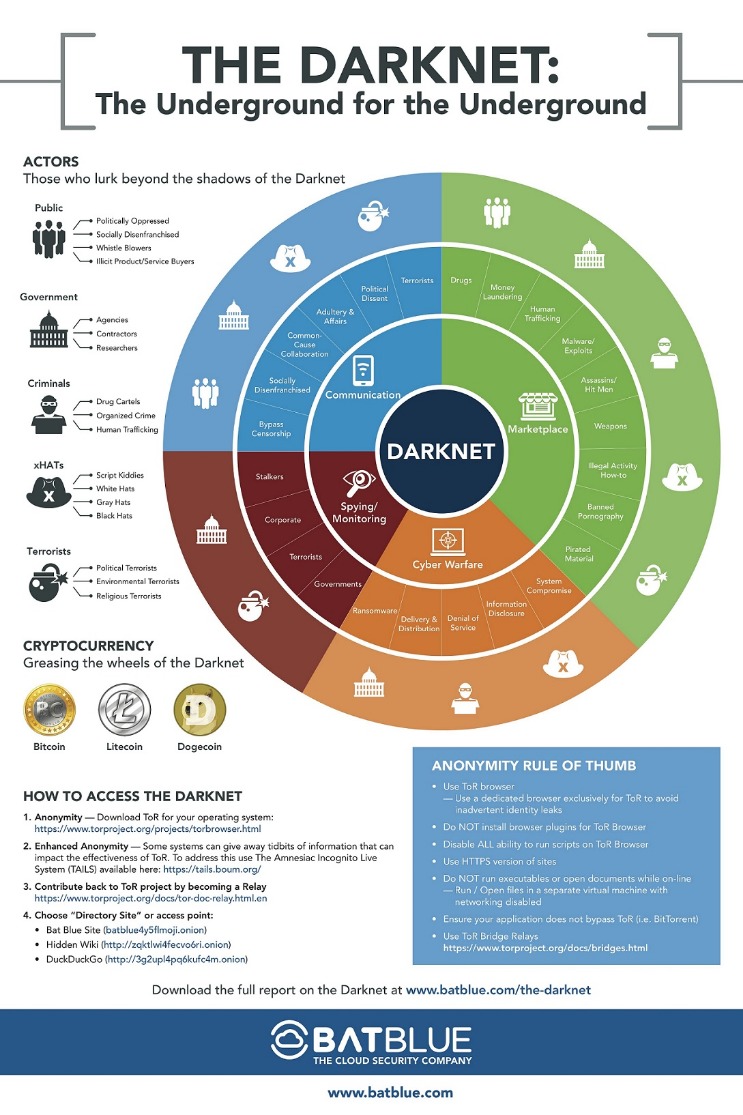
The Onion Project, or TOR is the predominant anonymous computer network. It works kind of like a VPN, but instead of routing your traffic through one remote server, it routes it through many random servers across the globe. The clearnet is the regular internet you’re used to using, where network traffic origins are fairly easy to pinpoint. The Camouflage Mode is intended for people living in countries with heavy internet censorship, like China. It will make your VPN activities seem like normal traffic, so you can use an uncensored internet.