
Security is the backbone of darknet markets, ensuring trust and anonymity in an ecosystem where traditional safeguards don’t apply. This section explores the security practices of our top 10 darknet rankings as of February 27, 2025, detailing how these platforms protect users, vendors, and transactions within their onion marketplaces. Understanding these measures is crucial for traders navigating the deep web markets, where a single breach can compromise anonymity and funds.
- The Tor Network provided a way to open safe communication channels for political dissidents, while also offering a channel for American intelligence operatives to communicate from around the globe.
- Radar Rundown Private search engines use the metasearch or proxy search model and the proprietary cr…
- In repressive regimes, darknets play a vital role in enabling free speech and access to uncensored information.
- Additionally, Tor exit nodes are often blocked by websites that don’t trust them, and Tor over VPN can’t do anything about that, either.
- In fact, there is an entire section of the dark web dedicated to pornographic content.
Explicit Content

Both rely on a peer-to-peer routing structure and layered encryption to make browsing private and anonymous. Tor over VPN also doesn’t protect users from malicious Tor exit nodes. Because Tor nodes are made up of volunteers, not all of them play by the rules. The final relay before your traffic goes to the destination website is known as the exit node. The exit node decrypts your traffic and thus can steal your personal information or inject malicious code.
Tor Bridges
Sure, you might come across listings for legit products like handcrafted jewelry or digital art, but those are few and far between. At KELA, we help you identify and mitigate risks by providing actionable intelligence from the darknet. Our solutions empower you to monitor illicit darknet marketplaces and track emerging threats, ensuring you can take proactive measures to protect your organization and reputation. The popular Silk Road was the first dark web marketplace that you could only access via the Tor Browser. The darknet markets are a hotbed for selling stolen personal information.

Launched in 2021, Torrez surged post-Hydra, growing vendors by 200+ in 2025, and survived a 2024 DDoS attack with enhanced defenses. Its top-tier rank reflects its vendor scale and trade strength, despite slight uptime and turnover challenges. The platform’s interface is a trader’s dream, with advanced filters, real-time tracking, and vendor ratings averaging 4.8/5 across 50,000+ reviews.
- Top vendors like “PharmaKing” and “MediSource” offer exclusive medications, driving Drughub’s 10% drug trade share, though its smaller pool limits variety outside pharma.
- Escrow reduces fraud by 25%—our top 10 average 94%+ success, with Alphabay at 99%, securing $20M monthly.
- Accessing any darknet marketplace is dangerous because it is known to be a hub for illegal trade.
- The platform allows buyers to review the vendor’s products and services, so it’s easy for them to decide if the vendor is reputable or just scamming them.
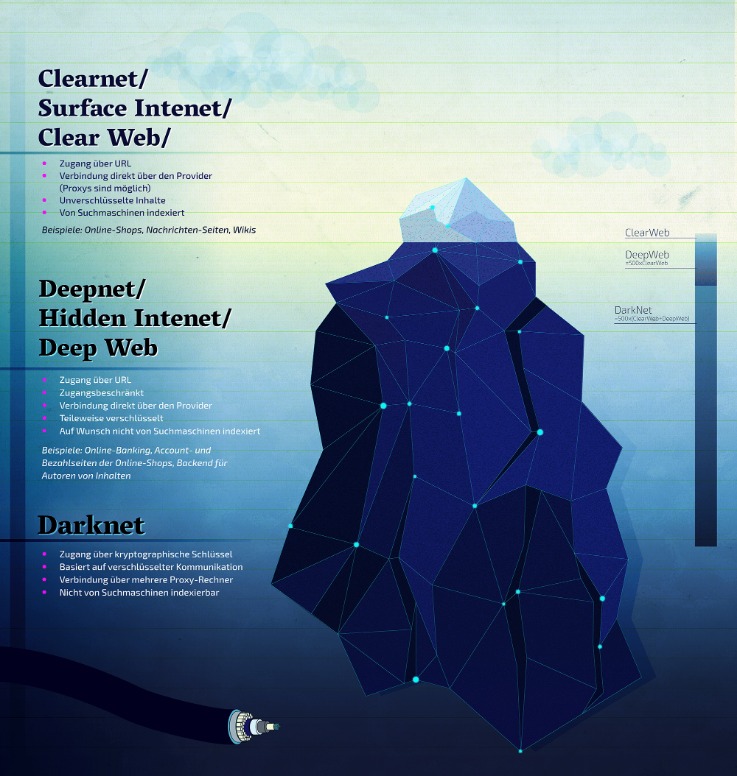
- Search engines like Google, Bing, and Yahoo can access just about 4% of the web.
Darknet Markets Links — 2025 Guide
This is where cybercriminals go to buy and sell things like stolen credit card numbers, personally identifiable information (PII), and even SSH login details. One thing that distinguishes BidenCash on the dark web, however, is how it markets itself. The marketplace supports multiple payment methods, including Bitcoin (BTC), Litecoin (LTC), and Cryptocheck. They add new batches of stolen data every other week, and there’s even a bidding system where buyers can place offers on new data batches as soon as they become available.

Secure Tor Access
Additionally, an identity theft monitoring service, such as Experian IdentityWorks℠, will look for your personal information in more databases and on the dark web. It also comes with identity theft insurance, which can help cover the cost of recovering from identity theft. Having JavaScript enabled on the dark web can cause havoc because it can reveal your IP address to your website. Also, previously, the Tor browser was vulnerable to JavaScript attacks as it provided hackers a pathway to track your activities by using the session details.
About Abacus Market
Okay, you’ve got the bitcoins in your wallet and you’ve encrypted your address with your vendors PGP key. Click “Buy…” then paste your encrypted message into the box and press “Confirm” for your order. The way this works is that bitcoins use a blockchain so that you can track where it’s been throughout its existence. So the idea is that if a vendor has their coins seized they can track the transactions back to you through the blockchain. In practice, the chances of this happening are minimal and tumbling coins is ultimately not necessary. It can’t be proved that you sent that money to them for anything illicit anyway.
Phishing Attacks
The only way in is through the use of special software that renders all users anonymous and untraceable. These marketplaces are full of risks (security, legal, ethical issues – all of them). But if you still decide to access these websites, for education or research purposes, make sure you stay cautious. From items like drugs, fake ID cards, and hacked bank accounts to more complex offerings like human trafficking, these sites carry all the illegal activities you can think of. Torzon market made its debut in September 2022, and ever since, it has been on an upward trajectory. In fact, it now features more than 11,600 illegal items, which include hacking tools, hard drugs, and all types of cybercrime services.
How KELA Cyber Supports You In Darknet Monitoring And Risk Mitigation
Search engines like Google, Bing, and Yahoo can access just about 4% of the web. Darknet is your best source for the latest hacking tools, hacker news, cyber security best practices, ethical hacking & pen-testing. Radar Rundown Hiding your IP address is one of the best ways to protect your online activities from … Radar Rundown Private search engines use the metasearch or proxy search model and the proprietary cr… Radar Rundown Free firewall software allow privacy ethusuiasts to secure their network and block mal…
They sell these files for just a fraction of the original cost on the surface web or even share freely, which makes them tempting for people looking for shortcuts. While it might be tempting, remember that downloading such content has serious legal and cybersecurity risks. This can include everything from full names, email logins, and passwords to credit card details, social security numbers, and bank account information. The cybercriminals trade even sensitive documents, such as medical records, passport information, and driver’s licenses.
Torrez Vs Tor2door
Like other marketplaces, ASAP Market also requires you to register for an account. However, the website has some security risks, and users experience glitches. However, in April 2022, this site went offline after American and German federal government law enforcement agencies seized the website servers.
This particular marketplace surfaced in the middle of 2017 and had remained active ever since. A VPN enhances your privacy and security by encrypting your internet traffic and masking your IP address, making it difficult for anyone to track your online activities on the dark web. Utilizing The Onion Router (Tor) network, these sites encrypt user data, providing layers of protection much like an onion.
Your Guide To Darknet Market Links – What You Need To Know
Get answers to the most pressing questions about darknet markets in 2025, tailored to our top 10 rankings as of February 27, 2025. This FAQ section addresses common concerns and curiosities from traders navigating onion marketplaces, crypto trading platforms, and dark pool trading hubs. Drughub’s 600+ vendors specialize almost exclusively in pharmaceuticals, with 90% of its 15,000+ listings dedicated to prescription drugs, recreational substances, and rare compounds.



